AWS
Cloud Security and Compliance provides support for the following use cases and Lacework features:
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | AWS Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | AWS Cloud Audit Logs |
| Vulnerability Management | Vulnerability Management Dashboard | ECR Agentless Workload Scanning |
| User Entity Behaviour Analytics (UEBA) | Kubernetes Audit Log Dashboard Kubernetes Anomaly Detection Kubernetes Audit Log Polygraph | EKS Audit |
See below for information on planning Lacework integrations and the specific use cases for each integration:
- Cloud Audit and Configuration
- Agentless Workload Scanning
- EKS Audit
- ECR
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | AWS Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | Cloud Audit Logs |
Standard Cloud Account Integration
Prerequisites 📎
Prerequisites
Before you can integrate your AWS cloud environment with Lacework, you must configure the following:
- SNS topic - An Amazon Simple Notification Service (SNS) topic is a logical access point that acts as a communication channel. A topic lets you group multiple endpoints, such as AWS, Amazon SQS, HTTP/S, or an email address. All CloudTrail integrations require an SNS topic. Lacework can use an existing SNS topic or create one if you have not added an SNS topic to an existing CloudTrail.
- SQS queue - Amazon Simple Queue Service (SQS) is a message queue service used by distributed applications to exchange messages through a polling model. SQS decouples sending and receiving components without requiring each component to be concurrently available. Used together, Amazon SNS and Amazon SQS can deliver messages to applications that require immediate notification of an event. Messages are also persisted in an Amazon SQS queue for other applications to process at a later time. All CloudTrail integrations require an SQS queue.
- S3 bucket - A bucket is a container for objects stored in Amazon S3. All CloudTrail integrations require an S3 bucket. Lacework can use an existing bucket or create one in the designated account.
- CloudTrail - AWS CloudTrail is an AWS service that helps you enable governance, compliance, and operational and risk auditing of your AWS account. Actions taken by a user, role, or an AWS service are recorded as events in CloudTrail. Lacework can use an existing CloudTrail or create a new trail.
- IAM cross-account role - A cross-account role is required to give Lacework access for assessments of cloud resource configurations and for analysis of CloudTrail events. The cross-account role is given the following policies:
- Lacework custom audit policy - A custom policy that enables read-only access to configuration resources.
- Lacework custom IAM policy - A custom policy that provides Lacework read-only access to ingest CloudTrail logs.
Ensure that your IAM cross-account role and S3 bucket are collocated in the same AWS account - whether you're trying to configure this manually, via CloudFormation, or Terraform. This is related to legacy AWS rules that govern access to objects created inside S3 buckets that are beyond Lacework’s control. Setting up cross-account access is not enough to work around this issue.
Architecture 📎
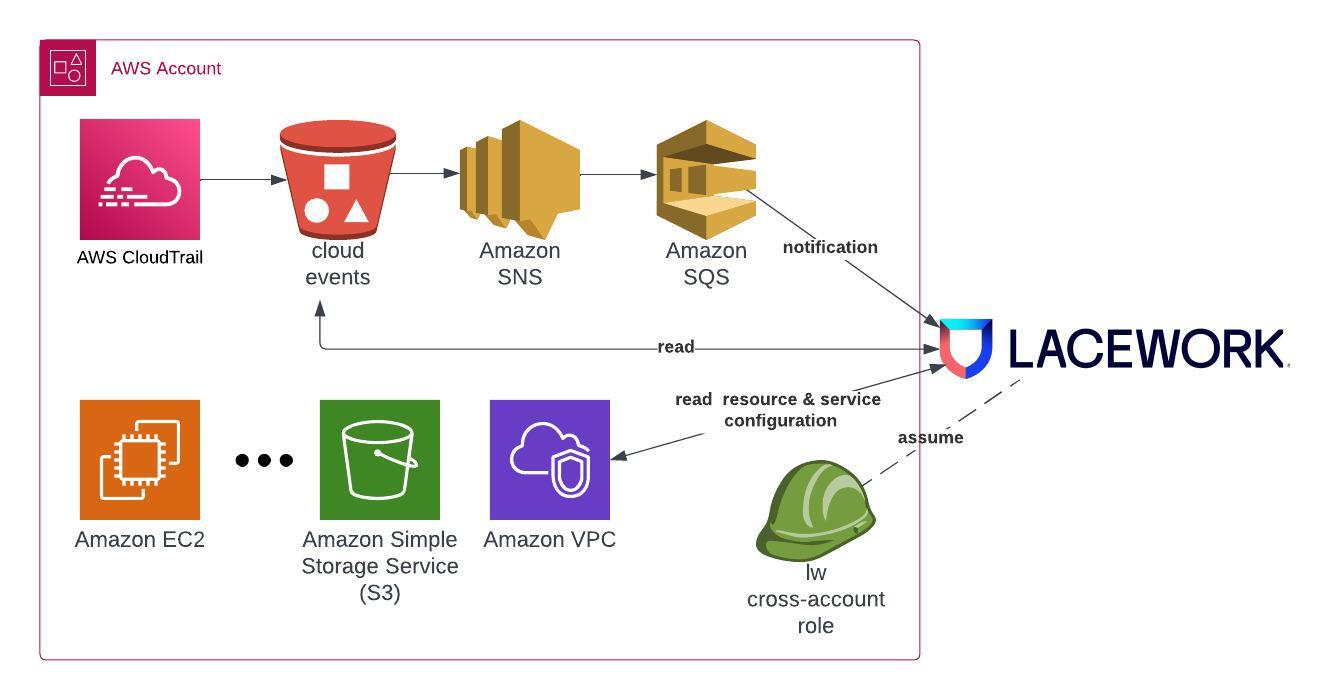
Architecture (S3 Bucket Notification) 📎
Permissions Required for Deployment 📎
Cloud Audit and Cloud Configuration
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"cloudtrail:CreateTrail",
"cloudtrail:DeleteTrail",
"cloudtrail:DescribeTrails",
"cloudtrail:GetEventSelectors",
"cloudtrail:GetTrailStatus",
"cloudtrail:ListTags",
"cloudtrail:StartLogging",
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:DeletePolicy",
"iam:DeleteRole",
"iam:DetachRolePolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListPolicyVersions",
"iam:ListRolePolicies",
"iam:TagRole",
"kms:CancelKeyDeletion",
"kms:Create*",
"kms:CreateKey",
"kms:Delete*",
"kms:Describe*",
"kms:DescribeKey",
"kms:Disable*",
"kms:Enable*",
"kms:Get*",
"kms:GetKeyPolicy",
"kms:GetKeyRotationStatus",
"kms:List*",
"kms:ListResourceTags",
"kms:Put*",
"kms:Revoke*",
"kms:ScheduleKeyDeletion",
"kms:TagResource",
"kms:Update*",
"s3:CreateBucket",
"s3:DeleteBucket",
"s3:DeleteBucket*",
"s3:DeleteBucketPolicy",
"s3:DeleteObject",
"s3:DeleteObjectVersion",
"s3:Get*",
"s3:GetAccelerateConfiguration",
"s3:GetBucketAcl",
"s3:GetBucketCORS",
"s3:GetBucketLogging",
"s3:GetBucketObjectLockConfiguration",
"s3:GetBucketOwnershipControls",
"s3:GetBucketPolicy",
"s3:GetBucketPublicAccessBlock",
"s3:GetBucketRequestPayment",
"s3:GetBucketTagging",
"s3:GetBucketVersioning",
"s3:GetBucketWebsite",
"s3:GetEncryptionConfiguration",
"s3:GetLifecycleConfiguration",
"s3:GetReplicationConfiguration",
"s3:List*",
"s3:ListBucket",
"s3:ListBucketVersions",
"s3:PutBucketAcl",
"s3:PutBucketLogging",
"s3:PutBucketNotification",
"s3:PutBucketOwnershipControls",
"s3:PutBucketPolicy",
"s3:PutBucketPublicAccessBlock",
"s3:PutBucketVersioning",
"s3:PutEncryptionConfiguration",
"sns:CreateTopic",
"sns:DeleteTopic",
"sns:GetSubscriptionAttributes",
"sns:GetTopicAttributes",
"sns:ListTagsForResource",
"sns:SetTopicAttributes",
"sns:Subscribe",
"sns:Unsubscribe",
"sqs:CreateQueue",
"sqs:DeleteQueue",
"sqs:GetQueueAttributes",
"sqs:ListQueueTags",
"sqs:SetQueueAttributes"
],
"Resource": "*"
}
]
}
- CloudTrail
- IAM
- KMS
- S3
- SNS
- SQS
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | cloudtrail:CreateTrail |
| <AWS_ACCOUNT_ID> | cloudtrail:DeleteTrail |
| <AWS_ACCOUNT_ID> | cloudtrail:DescribeTrails |
| <AWS_ACCOUNT_ID> | cloudtrail:GetEventSelectors |
| <AWS_ACCOUNT_ID> | cloudtrail:GetTrailStatus |
| <AWS_ACCOUNT_ID> | cloudtrail:ListTags |
| <AWS_ACCOUNT_ID> | cloudtrail:StartLogging |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:CreatePolicy |
| <AWS_ACCOUNT_ID> | iam:CreateRole |
| <AWS_ACCOUNT_ID> | iam:DeletePolicy |
| <AWS_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_ACCOUNT_ID> | iam:DetachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicyVersion |
| <AWS_ACCOUNT_ID> | iam:GetRole |
| <AWS_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_ACCOUNT_ID> | iam:ListPolicyVersions |
| <AWS_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_ACCOUNT_ID> | iam:TagRole |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | kms:CancelKeyDeletion |
| <AWS_ACCOUNT_ID> | kms:Create* |
| <AWS_ACCOUNT_ID> | kms:CreateKey |
| <AWS_ACCOUNT_ID> | kms:Delete* |
| <AWS_ACCOUNT_ID> | kms:Describe* |
| <AWS_ACCOUNT_ID> | kms:DescribeKey |
| <AWS_ACCOUNT_ID> | kms:Disable* |
| <AWS_ACCOUNT_ID> | kms:Enable* |
| <AWS_ACCOUNT_ID> | kms:Get* |
| <AWS_ACCOUNT_ID> | kms:GetKeyPolicy |
| <AWS_ACCOUNT_ID> | kms:GetKeyRotationStatus |
| <AWS_ACCOUNT_ID> | kms:List* |
| <AWS_ACCOUNT_ID> | kms:ListResourceTags |
| <AWS_ACCOUNT_ID> | kms:Put* |
| <AWS_ACCOUNT_ID> | kms:Revoke* |
| <AWS_ACCOUNT_ID> | kms:ScheduleKeyDeletion |
| <AWS_ACCOUNT_ID> | kms:TagResource |
| <AWS_ACCOUNT_ID> | kms:Update* |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | s3:CreateBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket* |
| <AWS_ACCOUNT_ID> | s3:DeleteBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:DeleteObject |
| <AWS_ACCOUNT_ID> | s3:DeleteObjectVersion |
| <AWS_ACCOUNT_ID> | s3:Get* |
| <AWS_ACCOUNT_ID> | s3:GetAccelerateConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketAcl |
| <AWS_ACCOUNT_ID> | s3:GetBucketCORS |
| <AWS_ACCOUNT_ID> | s3:GetBucketLogging |
| <AWS_ACCOUNT_ID> | s3:GetBucketObjectLockConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:GetBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:GetBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:GetBucketRequestPayment |
| <AWS_ACCOUNT_ID> | s3:GetBucketTagging |
| <AWS_ACCOUNT_ID> | s3:GetBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:GetBucketWebsite |
| <AWS_ACCOUNT_ID> | s3:GetEncryptionConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetLifecycleConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetReplicationConfiguration |
| <AWS_ACCOUNT_ID> | s3:List* |
| <AWS_ACCOUNT_ID> | s3:ListBucket |
| <AWS_ACCOUNT_ID> | s3:ListBucketVersions |
| <AWS_ACCOUNT_ID> | s3:PutBucketAcl |
| <AWS_ACCOUNT_ID> | s3:PutBucketLogging |
| <AWS_ACCOUNT_ID> | s3:PutBucketNotification |
| <AWS_ACCOUNT_ID> | s3:PutBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:PutBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:PutBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:PutBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:PutEncryptionConfiguration |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | sns:CreateTopic |
| <AWS_ACCOUNT_ID> | sns:DeleteTopic |
| <AWS_ACCOUNT_ID> | sns:GetSubscriptionAttributes |
| <AWS_ACCOUNT_ID> | sns:GetTopicAttributes |
| <AWS_ACCOUNT_ID> | sns:ListTagsForResource |
| <AWS_ACCOUNT_ID> | sns:SetTopicAttributes |
| <AWS_ACCOUNT_ID> | sns:Subscribe |
| <AWS_ACCOUNT_ID> | sns:Unsubscribe |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | sqs:CreateQueue |
| <AWS_ACCOUNT_ID> | sqs:DeleteQueue |
| <AWS_ACCOUNT_ID> | sqs:GetQueueAttributes |
| <AWS_ACCOUNT_ID> | sqs:ListQueueTags |
| <AWS_ACCOUNT_ID> | sqs:SetQueueAttributes |
Permissions Used in Operation 📎
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lacework-ct-iam-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"<EXTERNAL_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lacework-ct-cross-acct-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":"s3:Get*",
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-ct-bucket-<UNIQUE_ID>\/*",
"Sid":"ReadLogFiles"
},
{
"Action":"kms:Decrypt",
"Effect":"Allow",
"Resource":"arn:aws:kms:us-east-1:<AWS_ACCOUNT_ID>:key\/<KMS_KEY_ID>",
"Sid":"DecryptLogFiles"
},
{
"Action":"kms:Decrypt",
"Effect":"Allow",
"Resource":"arn:aws:kms:us-east-1:<AWS_ACCOUNT_ID>:key\/<KMS_KEY_ID>",
"Sid":"DecryptQueueFiles"
},
{
"Action":"iam:ListAccountAliases",
"Effect":"Allow",
"Resource":"*",
"Sid":"GetAccountAlias"
},
{
"Action":"s3:ListBucket",
"Condition":{
"StringLike":{
"s3:prefix":"*AWSLogs\/"
}
},
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-ct-bucket-<UNIQUE_ID>",
"Sid":"ListLogFiles"
},
{
"Action":[
"sqs:ReceiveMessage",
"sqs:GetQueueUrl",
"sqs:GetQueueAttributes",
"sqs:DeleteMessage"
],
"Effect":"Allow",
"Resource":"arn:aws:sqs:us-east-1:<AWS_ACCOUNT_ID>:lacework-ct-sqs-<UNIQUE_ID>",
"Sid":"ConsumeNotifications"
},
{
"Action":[
"sns:ListTopics",
"sns:ListSubscriptions",
"sns:GetTopicAttributes",
"s3:GetBucketPolicy",
"s3:GetBucketLocation",
"cloudtrail:GetTrailStatus",
"cloudtrail:DescribeTrails"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"Debug"
}
],
"Version":"2012-10-17"
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lw-iam-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lwaudit-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":"ec2:GetEbsEncryptionByDefault",
"Effect":"Allow",
"Resource":"*",
"Sid":"GetEbsEncryptionByDefault"
},
{
"Action":"s3:GetBucketPublicAccessBlock",
"Effect":"Allow",
"Resource":"*",
"Sid":"GetBucketPublicAccessBlock"
},
{
"Action":[
"elasticfilesystem:DescribeReplicationConfigurations",
"elasticfilesystem:DescribeLifecycleConfiguration",
"elasticfilesystem:DescribeFileSystemPolicy",
"elasticfilesystem:DescribeBackupPolicy",
"elasticfilesystem:DescribeAccountPreferences",
"elasticfilesystem:DescribeAccessPoints"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"EFS"
},
{
"Action":[
"elasticmapreduce:ListInstanceGroups",
"elasticmapreduce:ListInstanceFleets",
"elasticmapreduce:ListBootstrapActions"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"EMR"
},
{
"Action":[
"sagemaker:GetModelPackageGroupPolicy",
"sagemaker:GetLineageGroupPolicy"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"SAGEMAKER"
}
],
"Version":"2012-10-17"
}
},
"arn:aws:iam::aws:policy\/SecurityAudit"
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lacework-ct-iam-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lw-iam-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
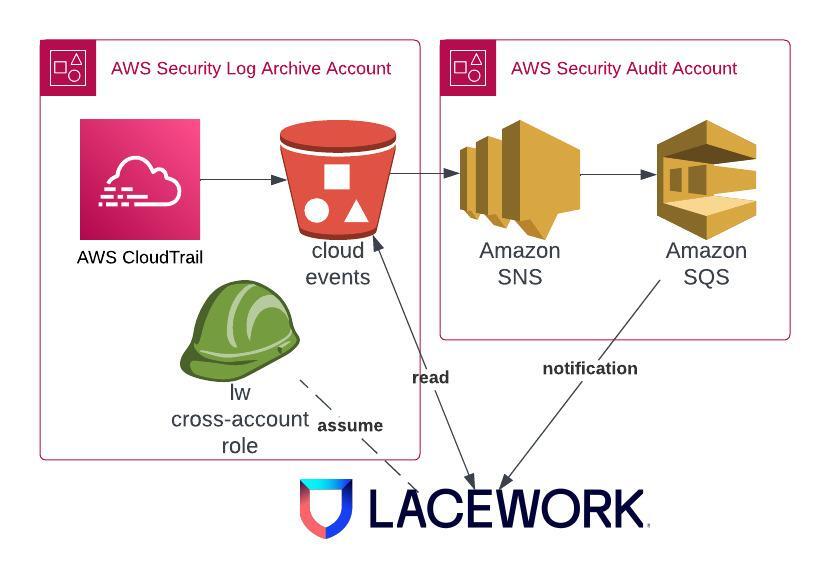
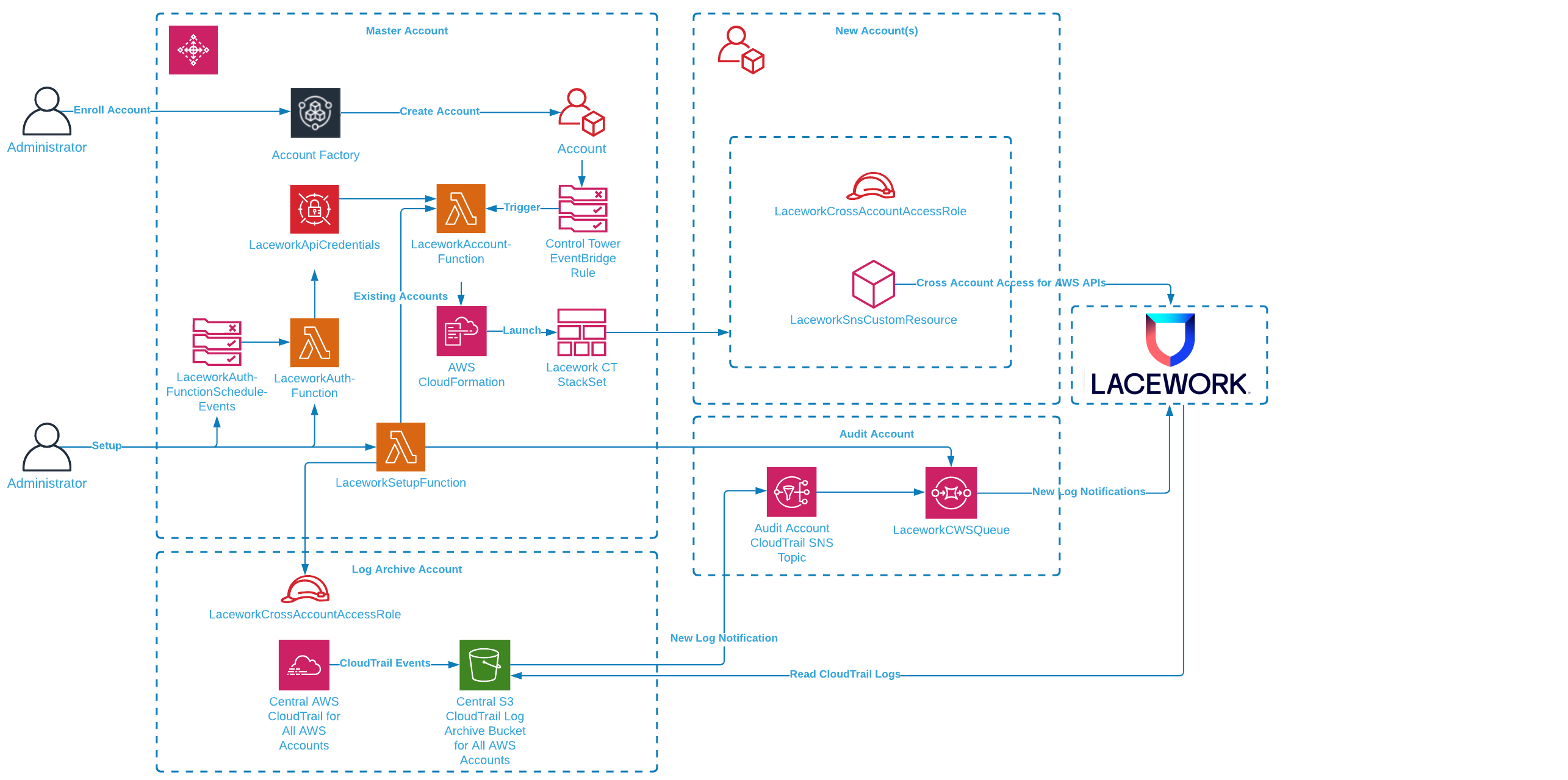
Cloud Audit Control Tower Integration
Cloud Audit via Control Tower 📎
Permissions Required for Cloud Audit Control Tower Deployment 📎
Cloud Audit Control Tower Integration
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
Audit Account
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"organizations:DescribeOrganization",
"sns:GetSubscriptionAttributes",
"sns:Subscribe",
"sns:Unsubscribe",
"sqs:CreateQueue",
"sqs:DeleteQueue",
"sqs:GetQueueAttributes",
"sqs:ListQueueTags",
"sqs:SetQueueAttributes"
],
"Resource": "*"
}
]
}
Log Archive Account
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:DeletePolicy",
"iam:DeleteRole",
"iam:DetachRolePolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListPolicyVersions",
"iam:ListRolePolicies",
"iam:TagRole"
],
"Resource": "*"
}
]
}
- IAM
- Organizations
- SNS
- SQS
| Scope | Permission |
|---|---|
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:CreatePolicy |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:CreateRole |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:DeletePolicy |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:DetachRolePolicy |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:GetPolicy |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:GetPolicyVersion |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:GetRole |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:ListPolicyVersions |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_LOG_ARCHIVE_ACCOUNT_ID> | iam:TagRole |
| Scope | Permission |
|---|---|
| <AWS_AUDIT_ACCOUNT_ID> | organizations:DescribeOrganization |
| Scope | Permission |
|---|---|
| <AWS_AUDIT_ACCOUNT_ID> | sns:GetSubscriptionAttributes |
| <AWS_AUDIT_ACCOUNT_ID> | sns:Subscribe |
| <AWS_AUDIT_ACCOUNT_ID> | sns:Unsubscribe |
| Scope | Permission |
|---|---|
| <AWS_AUDIT_ACCOUNT_ID> | sqs:CreateQueue |
| <AWS_AUDIT_ACCOUNT_ID> | sqs:DeleteQueue |
| <AWS_AUDIT_ACCOUNT_ID> | sqs:GetQueueAttributes |
| <AWS_AUDIT_ACCOUNT_ID> | sqs:ListQueueTags |
| <AWS_AUDIT_ACCOUNT_ID> | sqs:SetQueueAttributes |
Permissions Used in Operation 📎
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lacework-ct-iam-<UNIQUE_ID>",
"Account":"<AWS_LOG_ARCHIVE_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lacework-ct-cross-acct-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":"s3:Get*",
"Effect":"Allow",
"Resource":"arn:aws:s3:::aws-controltower-logs-<AWS_LOG_ARCHIVE_ACCOUNT_ID>-us-east-1\/<AWS_ORG_ID>\/*AWSLogs\/*",
"Sid":"ReadLogFiles"
},
{
"Action":"iam:ListAccountAliases",
"Effect":"Allow",
"Resource":"*",
"Sid":"GetAccountAlias"
},
{
"Action":"s3:ListBucket",
"Condition":{
"StringLike":{
"s3:prefix":[
"*AWSLogs\/"
]
}
},
"Effect":"Allow",
"Resource":"arn:aws:s3:::aws-controltower-logs-<AWS_LOG_ARCHIVE_ACCOUNT_ID>-us-east-1\/<AWS_ORG_ID>\/*AWSLogs\/*",
"Sid":"ListLogFiles"
},
{
"Action":[
"sqs:ReceiveMessage",
"sqs:GetQueueUrl",
"sqs:GetQueueAttributes",
"sqs:DeleteMessage"
],
"Effect":"Allow",
"Resource":"arn:aws:sqs:us-east-1:<AWS_AUDIT_ACCOUNT_ID>:lacework-ct-sqs-<UNIQUE_ID>",
"Sid":"ConsumeNotifications"
},
{
"Action":[
"sns:ListTopics",
"sns:ListSubscriptionsByTopic",
"sns:ListSubscriptions",
"sns:GetTopicAttributes",
"sns:GetSubscriptionAttributes",
"s3:ListAllMyBuckets",
"s3:GetBucketPolicy",
"s3:GetBucketLogging",
"s3:GetBucketLocation",
"s3:GetBucketAcl",
"cloudtrail:ListPublicKeys",
"cloudtrail:GetTrailStatus",
"cloudtrail:GetTrail",
"cloudtrail:DescribeTrails"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"Debug"
}
],
"Version":"2012-10-17"
}
}
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lacework-ct-iam-<UNIQUE_ID> | <AWS_LOG_ARCHIVE_ACCOUNT_ID> | { | [ |
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | Agentless Workload Scanning |
Prerequisites 📎
Support Matrix for Agentless Workload Scanning
Supported Cloud Providers
- Amazon Web Services (AWS)
- Google Cloud Platform (GCP)
Supported Operating Systems
x86 Architecture
| Operating System | Versions |
|---|---|
| Alma Linux | 8.7, 9.1 |
| Alpine Linux (General beta support) | 3.10, 3.11, 3.12, 3.13, 3.14, 3.15, 3.16.2 |
| Amazon Linux | 2, 2022, 2023 |
| Amazon Linux AMI | 2016.03, 2016.09, 2017.03, 2017.09, 2018.03 |
| CentOS | 6.x, 7.x, 8.x, 9.x |
| Debian | 9, 10, 11, 12 |
| Fedora | 30, 31, 32, 33, 34, 35 |
| Kali GNU/Linux Rolling | Rolling distribution (up to Kali 2022.3) |
| Oracle Linux | 8.3, 8.4, 8.5 |
| Red Hat Enterprise Linux | 7.9, 8.0, 8.1.0, 8.2, 8.3, 8.4, 8.5, 8.6, 8.7, 8.8, 9 |
| Red Hat OpenShift | 4.9 |
| Red Hat OpenShift Service on AWS | 4.9, 4.10, 4.11, 4.12 |
| Rocky Linux | 8.4, 8.5, 8.6, 8.7, 9.0, 9.1 |
| SUSE | 11.4.20, 12 SP1, 12 SP5, 15, 15 SP1, 15 SP2, 15 SP3, 15 SP4 |
| Ubuntu | 14.04, 16.04, 16.10, 17.04, 17.10, 18.04, 18.10, 19.04, 19.10, 20.04, 21.04, 21.10 22.04 LTS (Jammy Jellyfish), 22.1, 23 |
ARM64 Architecture
Lacework supports the following ARM-based operating systems, including AWS Graviton and Graviton2 ARM-based instances.
| Operating System | Versions |
|---|---|
| Alma Linux | 8.7, 9.1 |
| Amazon Linux | 2, 2022, 2023 |
| CentOS | 6.10, 8.2, 9 |
| Debian | 9, 10, 11, 12 |
| Fedora | 30, 31, 32, 33, 34, 35 |
| Flatcar | 2605.x (amd64 only) |
| Red Hat Enterprise Linux | 7.9, 8.0, 8.1, 8.2, 8.3, 8.4, 8.5, 8.6, 8.7, 8.8, 9 |
| Red Hat OpenShift | 4.9 |
| Red Hat OpenShift Service on AWS | 4.9, 4.10, 4.11, 4.12 |
| Rocky Linux | 8.4, 8.5, 8.6, 8.7, 9.0, 9.1 |
| SUSE | 12 SP5, 15 SP2, 15 SP3, 15 SP4 |
| Ubuntu | 16.04, 17.04, 18.04, 19.04, 20.04, 21.04, 21.10 22.04 LTS (Jammy Jellyfish), 22.1, 23 |
Supported Container Image Formats
| Container image format | Directories scanned |
|---|---|
| Docker | /var/lib/docker /var/snap/docker/common/var-lib-docker /var/lib/system-docker |
| Open Container Initiative (OCI) | /var/lib/containers/storage /home/<username>/.local/share/containers/storage |
| Containerd | /var/lib/containerd |
Supported File Systems
- Btrfs
- ext2
- ext3
- ext4
- XFS
- ReiserFS
Supported Language Libraries and Package Managers
See the following sections:
Architecture 📎
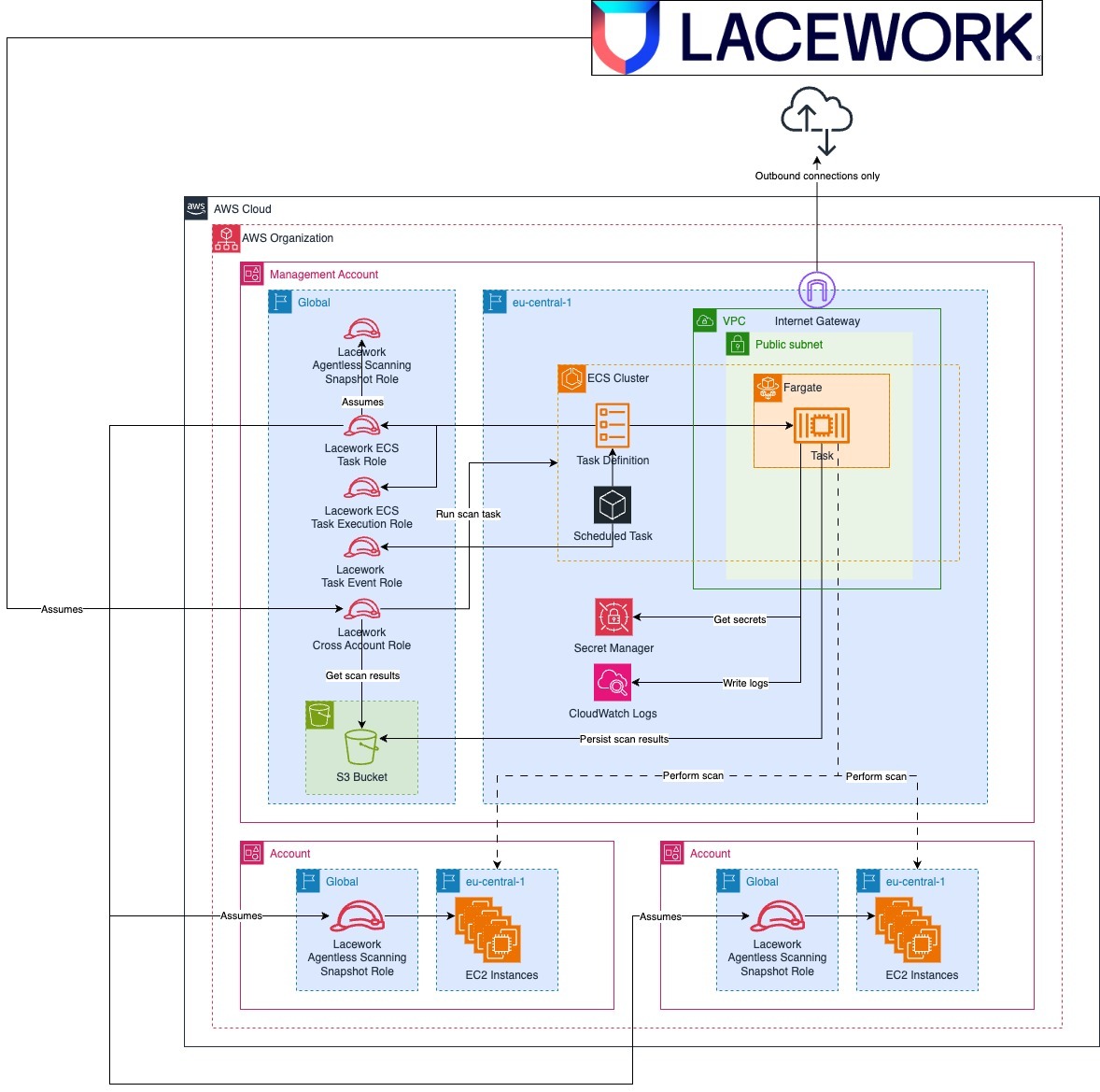
Single Account Integration
Permissions Required for Deployment 📎
Agentless Workload Scanning
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"ec2:AssociateRouteTable",
"ec2:AttachInternetGateway",
"ec2:AuthorizeSecurityGroupEgress",
"ec2:CreateInternetGateway",
"ec2:CreateNetworkAclEntry",
"ec2:CreateRoute",
"ec2:CreateRouteTable",
"ec2:CreateSecurityGroup",
"ec2:CreateSubnet",
"ec2:CreateTags",
"ec2:CreateVpc",
"ec2:DeleteInternetGateway",
"ec2:DeleteNetworkAclEntry",
"ec2:DeleteRoute",
"ec2:DeleteRouteTable",
"ec2:DeleteSecurityGroup",
"ec2:DeleteSubnet",
"ec2:DeleteVpc",
"ec2:DescribeInternetGateways",
"ec2:DescribeNetworkAcls",
"ec2:DescribeNetworkInterfaces",
"ec2:DescribeRouteTables",
"ec2:DescribeSecurityGroupRules",
"ec2:DescribeSecurityGroups",
"ec2:DescribeSubnets",
"ec2:DescribeVpcAttribute",
"ec2:DescribeVpcClassicLink",
"ec2:DescribeVpcClassicLinkDnsSupport",
"ec2:DescribeVpcs",
"ec2:DetachInternetGateway",
"ec2:DisassociateRouteTable",
"ec2:ModifyVpcAttribute",
"ec2:ReplaceNetworkAclAssociation",
"ec2:RevokeSecurityGroupEgress",
"ec2:RevokeSecurityGroupIngress",
"ecs:CreateCluster",
"ecs:DeleteCluster",
"ecs:DeregisterTaskDefinition",
"ecs:DescribeClusters",
"ecs:DescribeTaskDefinition",
"ecs:PutClusterCapacityProviders",
"ecs:RegisterTaskDefinition",
"events:DeleteRule",
"events:DescribeRule",
"events:ListTagsForResource",
"events:ListTargetsByRule",
"events:PutRule",
"events:PutTargets",
"events:RemoveTargets",
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:DeletePolicy",
"iam:DeleteRole",
"iam:DeleteRolePolicy",
"iam:DetachRolePolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListPolicyVersions",
"iam:ListRolePolicies",
"iam:PassRole",
"iam:PutRolePolicy",
"iam:TagRole",
"logs:CreateLogGroup",
"logs:DeleteLogGroup",
"logs:DescribeLogGroups",
"logs:ListTagsLogGroup",
"logs:PutRetentionPolicy",
"s3:CreateBucket",
"s3:DeleteBucket",
"s3:DeleteBucket*",
"s3:DeleteBucketPolicy",
"s3:DeleteObject",
"s3:DeleteObjectVersion",
"s3:Get*",
"s3:GetAccelerateConfiguration",
"s3:GetBucketAcl",
"s3:GetBucketCORS",
"s3:GetBucketLogging",
"s3:GetBucketObjectLockConfiguration",
"s3:GetBucketOwnershipControls",
"s3:GetBucketPolicy",
"s3:GetBucketPublicAccessBlock",
"s3:GetBucketRequestPayment",
"s3:GetBucketTagging",
"s3:GetBucketVersioning",
"s3:GetBucketWebsite",
"s3:GetEncryptionConfiguration",
"s3:GetLifecycleConfiguration",
"s3:GetReplicationConfiguration",
"s3:List*",
"s3:ListBucket",
"s3:ListBucketVersions",
"s3:PutBucketAcl",
"s3:PutBucketLogging",
"s3:PutBucketNotification",
"s3:PutBucketOwnershipControls",
"s3:PutBucketPolicy",
"s3:PutBucketPublicAccessBlock",
"s3:PutBucketTagging",
"s3:PutBucketVersioning",
"s3:PutEncryptionConfiguration",
"s3:PutLifecycleConfiguration",
"secretsmanager:CreateSecret",
"secretsmanager:DeleteSecret",
"secretsmanager:DescribeSecret",
"secretsmanager:GetResourcePolicy",
"secretsmanager:GetSecretValue",
"secretsmanager:PutSecretValue"
],
"Resource": "*"
}
]
}
- EC2
- ECS
- Events
- IAM
- Logs
- S3
- Secrets Manager
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | ec2:AssociateRouteTable |
| <AWS_ACCOUNT_ID> | ec2:AttachInternetGateway |
| <AWS_ACCOUNT_ID> | ec2:AuthorizeSecurityGroupEgress |
| <AWS_ACCOUNT_ID> | ec2:CreateInternetGateway |
| <AWS_ACCOUNT_ID> | ec2:CreateNetworkAclEntry |
| <AWS_ACCOUNT_ID> | ec2:CreateRoute |
| <AWS_ACCOUNT_ID> | ec2:CreateRouteTable |
| <AWS_ACCOUNT_ID> | ec2:CreateSecurityGroup |
| <AWS_ACCOUNT_ID> | ec2:CreateSubnet |
| <AWS_ACCOUNT_ID> | ec2:CreateTags |
| <AWS_ACCOUNT_ID> | ec2:CreateVpc |
| <AWS_ACCOUNT_ID> | ec2:DeleteInternetGateway |
| <AWS_ACCOUNT_ID> | ec2:DeleteNetworkAclEntry |
| <AWS_ACCOUNT_ID> | ec2:DeleteRoute |
| <AWS_ACCOUNT_ID> | ec2:DeleteRouteTable |
| <AWS_ACCOUNT_ID> | ec2:DeleteSecurityGroup |
| <AWS_ACCOUNT_ID> | ec2:DeleteSubnet |
| <AWS_ACCOUNT_ID> | ec2:DeleteVpc |
| <AWS_ACCOUNT_ID> | ec2:DescribeInternetGateways |
| <AWS_ACCOUNT_ID> | ec2:DescribeNetworkAcls |
| <AWS_ACCOUNT_ID> | ec2:DescribeNetworkInterfaces |
| <AWS_ACCOUNT_ID> | ec2:DescribeRouteTables |
| <AWS_ACCOUNT_ID> | ec2:DescribeSecurityGroupRules |
| <AWS_ACCOUNT_ID> | ec2:DescribeSecurityGroups |
| <AWS_ACCOUNT_ID> | ec2:DescribeSubnets |
| <AWS_ACCOUNT_ID> | ec2:DescribeVpcAttribute |
| <AWS_ACCOUNT_ID> | ec2:DescribeVpcClassicLink |
| <AWS_ACCOUNT_ID> | ec2:DescribeVpcClassicLinkDnsSupport |
| <AWS_ACCOUNT_ID> | ec2:DescribeVpcs |
| <AWS_ACCOUNT_ID> | ec2:DetachInternetGateway |
| <AWS_ACCOUNT_ID> | ec2:DisassociateRouteTable |
| <AWS_ACCOUNT_ID> | ec2:ModifyVpcAttribute |
| <AWS_ACCOUNT_ID> | ec2:ReplaceNetworkAclAssociation |
| <AWS_ACCOUNT_ID> | ec2:RevokeSecurityGroupEgress |
| <AWS_ACCOUNT_ID> | ec2:RevokeSecurityGroupIngress |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | ecs:CreateCluster |
| <AWS_ACCOUNT_ID> | ecs:DeleteCluster |
| <AWS_ACCOUNT_ID> | ecs:DeregisterTaskDefinition |
| <AWS_ACCOUNT_ID> | ecs:DescribeClusters |
| <AWS_ACCOUNT_ID> | ecs:DescribeTaskDefinition |
| <AWS_ACCOUNT_ID> | ecs:PutClusterCapacityProviders |
| <AWS_ACCOUNT_ID> | ecs:RegisterTaskDefinition |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | events:DeleteRule |
| <AWS_ACCOUNT_ID> | events:DescribeRule |
| <AWS_ACCOUNT_ID> | events:ListTagsForResource |
| <AWS_ACCOUNT_ID> | events:ListTargetsByRule |
| <AWS_ACCOUNT_ID> | events:PutRule |
| <AWS_ACCOUNT_ID> | events:PutTargets |
| <AWS_ACCOUNT_ID> | events:RemoveTargets |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:CreatePolicy |
| <AWS_ACCOUNT_ID> | iam:CreateRole |
| <AWS_ACCOUNT_ID> | iam:DeletePolicy |
| <AWS_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_ACCOUNT_ID> | iam:DeleteRolePolicy |
| <AWS_ACCOUNT_ID> | iam:DetachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicyVersion |
| <AWS_ACCOUNT_ID> | iam:GetRole |
| <AWS_ACCOUNT_ID> | iam:GetRolePolicy |
| <AWS_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_ACCOUNT_ID> | iam:ListPolicyVersions |
| <AWS_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_ACCOUNT_ID> | iam:PassRole |
| <AWS_ACCOUNT_ID> | iam:PutRolePolicy |
| <AWS_ACCOUNT_ID> | iam:TagRole |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | logs:CreateLogGroup |
| <AWS_ACCOUNT_ID> | logs:DeleteLogGroup |
| <AWS_ACCOUNT_ID> | logs:DescribeLogGroups |
| <AWS_ACCOUNT_ID> | logs:ListTagsLogGroup |
| <AWS_ACCOUNT_ID> | logs:PutRetentionPolicy |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | s3:CreateBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket* |
| <AWS_ACCOUNT_ID> | s3:DeleteBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:DeleteObject |
| <AWS_ACCOUNT_ID> | s3:DeleteObjectVersion |
| <AWS_ACCOUNT_ID> | s3:Get* |
| <AWS_ACCOUNT_ID> | s3:GetAccelerateConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketAcl |
| <AWS_ACCOUNT_ID> | s3:GetBucketCORS |
| <AWS_ACCOUNT_ID> | s3:GetBucketLogging |
| <AWS_ACCOUNT_ID> | s3:GetBucketObjectLockConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:GetBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:GetBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:GetBucketRequestPayment |
| <AWS_ACCOUNT_ID> | s3:GetBucketTagging |
| <AWS_ACCOUNT_ID> | s3:GetBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:GetBucketWebsite |
| <AWS_ACCOUNT_ID> | s3:GetEncryptionConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetLifecycleConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetReplicationConfiguration |
| <AWS_ACCOUNT_ID> | s3:List* |
| <AWS_ACCOUNT_ID> | s3:ListBucket |
| <AWS_ACCOUNT_ID> | s3:ListBucketVersions |
| <AWS_ACCOUNT_ID> | s3:PutBucketAcl |
| <AWS_ACCOUNT_ID> | s3:PutBucketLogging |
| <AWS_ACCOUNT_ID> | s3:PutBucketNotification |
| <AWS_ACCOUNT_ID> | s3:PutBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:PutBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:PutBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:PutBucketTagging |
| <AWS_ACCOUNT_ID> | s3:PutBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:PutEncryptionConfiguration |
| <AWS_ACCOUNT_ID> | s3:PutLifecycleConfiguration |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | secretsmanager:CreateSecret |
| <AWS_ACCOUNT_ID> | secretsmanager:DeleteSecret |
| <AWS_ACCOUNT_ID> | secretsmanager:DescribeSecret |
| <AWS_ACCOUNT_ID> | secretsmanager:GetResourcePolicy |
| <AWS_ACCOUNT_ID> | secretsmanager:GetSecretValue |
| <AWS_ACCOUNT_ID> | secretsmanager:PutSecretValue |
Permissions Used in Operation 📎
Agentless Workload Scanning
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-cross-account-role-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"ECSTaskManagement",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"ecs:StopTask",
"ecs:RunTask"
],
"Condition":{
"ArnEquals":{
"ecs:cluster":"arn:aws:ecs:*:*:cluster\/lacework-agentless-scanning-cluster-<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Resource":[
"arn:aws:ecs:*:*:task\/lacework-agentless-scanning-cluster-<UNIQUE_ID>\/*",
"arn:aws:ecs:*:*:task-definition\/lacework-agentless-scanning-cluster-<UNIQUE_ID>:*"
],
"Sid":"AllowEcsStopTask"
},
{
"Action":"iam:PassRole",
"Effect":"Allow",
"Resource":[
"arn:aws:iam::*:role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>",
"arn:aws:iam::*:role\/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID>"
],
"Sid":"AllowEcsTaskManagementPassRole"
},
{
"Action":"ec2:DescribeSubnets",
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"arn:aws:ec2:*:*:subnet\/subnet-*",
"Sid":"AllowEcsTaskSubnetLookup"
}
]
}
},
{
"name":"S3WriteAllowPolicy",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"s3:PutBucketTagging",
"s3:ListBucket",
"s3:GetBucketTagging",
"s3:GetBucketLocation"
],
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>",
"Sid":"ListAndTagBucket"
},
{
"Action":[
"s3:PutObject",
"s3:GetObject",
"s3:DeleteObject"
],
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>\/*",
"Sid":"PutGetDeleteObjectsInBucket"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/service-role\/lacework-agentless-scanning-task-event-role-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"events.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
"arn:aws:iam::aws:policy\/service-role\/AmazonEC2ContainerServiceEventsRole"
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"ecs-tasks.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
"arn:aws:iam::aws:policy\/service-role\/AmazonECSTaskExecutionRolePolicy",
{
"name":"AllowCloudWatch",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"logs:PutLogEvents",
"logs:CreateLogStream",
"logs:CreateLogGroup"
],
"Effect":"Allow",
"Resource":"arn:aws:logs:*:*:log-group:\/ecs\/lacework-agentless-scanning-*",
"Sid":"AllowLoggingToCloudWatch"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"ecs-tasks.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lacework-agentless-scanning-task-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":"s3:*",
"Effect":"Allow",
"Resource":[
"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>\/*",
"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>"
],
"Sid":"AllowControlOfBucket"
},
{
"Action":[
"ecs:UntagResource",
"ecs:TagResource",
"ecs:ListTagsForResource"
],
"Condition":{
"StringLike":{
"ecs:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"AllowTagECSCluster"
},
{
"Action":[
"events:ListTargetsByRule",
"events:ListTagsForResource",
"events:ListRules",
"events:ListRuleNamesByTarget",
"events:DescribeRule"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"AllowListRules"
},
{
"Action":[
"events:RemoveTargets",
"events:PutTargets",
"events:EnableRule",
"events:DisableRule"
],
"Effect":"Allow",
"Resource":"arn:aws:events:*:*:rule\/lacework-agentless-scanning-periodic-trigger-<UNIQUE_ID>",
"Sid":"AllowUpdateRule"
},
{
"Action":[
"secretsmanager:ListSecretVersionIds",
"secretsmanager:GetSecretValue",
"secretsmanager:GetResourcePolicy"
],
"Effect":"Allow",
"Resource":"arn:aws:secretsmanager:us-east-1:<AWS_ACCOUNT_ID>:secret:lacework-agentless-scanning-secret-<UNIQUE_ID>",
"Sid":"AllowReadFromSecretsManager"
},
{
"Action":"ec2:Describe*",
"Effect":"Allow",
"Resource":"*",
"Sid":"DescribeInstances"
},
{
"Action":"ec2:CreateSnapshot",
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshots"
},
{
"Action":"ec2:CreateTags",
"Condition":{
"StringEquals":{
"ec2:CreateAction":"CreateSnapshot"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshotTags"
},
{
"Action":[
"ec2:ResetSnapshotAttribute",
"ec2:ModifySnapshotAttribute",
"ec2:DeleteSnapshot",
"ebs:ListSnapshotBlocks",
"ebs:ListChangedBlocks",
"ebs:GetSnapshotBlock",
"ebs:CompleteSnapshot"
],
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotManagement"
},
{
"Action":[
"ecs:StopTask",
"ecs:StartTask",
"ecs:RunTask",
"ecs:ListTasks",
"ecs:Describe*"
],
"Condition":{
"ArnEquals":{
"ecs:cluster":"arn:aws:ecs:*:*:cluster\/lacework-agentless-scanning-cluster-<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"TaskManagement"
},
{
"Action":[
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:Encrypt",
"kms:DescribeKey",
"kms:Decrypt"
],
"Condition":{
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryption"
},
{
"Action":"kms:CreateGrant",
"Condition":{
"Bool":{
"kms:GrantIsForAWSResource":"true"
},
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryptionGrants"
},
{
"Action":[
"sts:AssumeRole",
"iam:PassRole"
],
"Condition":{
"StringLike":{
"iam:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"PassRoleToTasks"
},
{
"Action":"sts:DecodeAuthorizationMessage",
"Effect":"Allow",
"Resource":"*",
"Sid":"DecodeErrorMessages"
},
{
"Action":[
"logs:GetLogEvents",
"logs:DescribeLogStreams"
],
"Effect":"Allow",
"Resource":"arn:aws:logs:*:*:log-group:\/ecs\/lacework-agentless-scanning-*",
"Sid":"ReadLogs"
}
],
"Version":"2012-10-17"
}
}
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lacework-agentless-scanning-cross-account-role-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/service-role/lacework-agentless-scanning-task-event-role-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-task-role-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
Organization Deployment
Permissions Required for Deployment 📎
Agentless Workload Scanning
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
Management Account
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"iam:CreateRole",
"iam:DeleteRole",
"iam:DeleteRolePolicy",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListRolePolicies",
"iam:PutRolePolicy",
"iam:TagRole",
"organizations:DescribeOrganization",
"organizations:ListAWSServiceAccessForOrganization",
"organizations:ListAccounts",
"organizations:ListRoots"
],
"Resource": "*"
}
]
}
Monitored Account
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"iam:CreateRole",
"iam:DeleteRole",
"iam:DeleteRolePolicy",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListRolePolicies",
"iam:PutRolePolicy",
"iam:TagRole"
],
"Resource": "*"
}
]
}
Scanning Account
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"ec2:AssociateRouteTable",
"ec2:AttachInternetGateway",
"ec2:AuthorizeSecurityGroupEgress",
"ec2:CreateInternetGateway",
"ec2:CreateNetworkAclEntry",
"ec2:CreateRoute",
"ec2:CreateRouteTable",
"ec2:CreateSecurityGroup",
"ec2:CreateSubnet",
"ec2:CreateTags",
"ec2:CreateVpc",
"ec2:DeleteNetworkAclEntry",
"ec2:DeleteRoute",
"ec2:DeleteRouteTable",
"ec2:DeleteSecurityGroup",
"ec2:DeleteSubnet",
"ec2:DescribeInternetGateways",
"ec2:DescribeNetworkAcls",
"ec2:DescribeNetworkInterfaces",
"ec2:DescribeRouteTables",
"ec2:DescribeSecurityGroupRules",
"ec2:DescribeSecurityGroups",
"ec2:DescribeSubnets",
"ec2:DescribeVpcAttribute",
"ec2:DescribeVpcClassicLink",
"ec2:DescribeVpcClassicLinkDnsSupport",
"ec2:DescribeVpcs",
"ec2:DetachInternetGateway",
"ec2:DisassociateRouteTable",
"ec2:ModifyVpcAttribute",
"ec2:ReplaceNetworkAclAssociation",
"ec2:RevokeSecurityGroupEgress",
"ec2:RevokeSecurityGroupIngress",
"ecs:CreateCluster",
"ecs:DeleteCluster",
"ecs:DeregisterTaskDefinition",
"ecs:DescribeClusters",
"ecs:DescribeTaskDefinition",
"ecs:PutClusterCapacityProviders",
"ecs:RegisterTaskDefinition",
"events:DeleteRule",
"events:DescribeRule",
"events:ListTagsForResource",
"events:ListTargetsByRule",
"events:PutRule",
"events:PutTargets",
"events:RemoveTargets",
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:GetRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:ListRolePolicies",
"iam:PassRole",
"iam:PutRolePolicy",
"iam:TagRole",
"logs:CreateLogGroup",
"logs:DeleteLogGroup",
"logs:DescribeLogGroups",
"logs:ListTagsLogGroup",
"logs:PutRetentionPolicy",
"s3:CreateBucket",
"s3:DeleteBucket*",
"s3:Get*",
"s3:GetAccelerateConfiguration",
"s3:GetBucketAcl",
"s3:GetBucketCORS",
"s3:GetBucketLogging",
"s3:GetBucketObjectLockConfiguration",
"s3:GetBucketOwnershipControls",
"s3:GetBucketPolicy",
"s3:GetBucketPublicAccessBlock",
"s3:GetBucketRequestPayment",
"s3:GetBucketTagging",
"s3:GetBucketVersioning",
"s3:GetBucketWebsite",
"s3:GetEncryptionConfiguration",
"s3:GetLifecycleConfiguration",
"s3:GetReplicationConfiguration",
"s3:List*",
"s3:ListBucket",
"s3:PutBucketAcl",
"s3:PutBucketLogging",
"s3:PutBucketNotification",
"s3:PutBucketOwnershipControls",
"s3:PutBucketPolicy",
"s3:PutBucketPublicAccessBlock",
"s3:PutBucketTagging",
"s3:PutBucketVersioning",
"s3:PutEncryptionConfiguration",
"s3:PutLifecycleConfiguration",
"secretsmanager:CreateSecret",
"secretsmanager:DescribeSecret",
"secretsmanager:GetResourcePolicy",
"secretsmanager:GetSecretValue",
"secretsmanager:PutSecretValue"
],
"Resource": "*"
}
]
}
- EC2
- ECS
- Events
- IAM
- Logs
- Organizations
- S3
- Secrets Manager
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:AssociateRouteTable |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:AttachInternetGateway |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:AuthorizeSecurityGroupEgress |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateInternetGateway |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateNetworkAclEntry |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateRoute |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateRouteTable |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateSecurityGroup |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateSubnet |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateTags |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:CreateVpc |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DeleteNetworkAclEntry |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DeleteRoute |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DeleteRouteTable |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DeleteSecurityGroup |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DeleteSubnet |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeInternetGateways |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeNetworkAcls |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeNetworkInterfaces |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeRouteTables |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeSecurityGroupRules |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeSecurityGroups |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeSubnets |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeVpcAttribute |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeVpcClassicLink |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeVpcClassicLinkDnsSupport |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DescribeVpcs |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DetachInternetGateway |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:DisassociateRouteTable |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:ModifyVpcAttribute |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:ReplaceNetworkAclAssociation |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:RevokeSecurityGroupEgress |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ec2:RevokeSecurityGroupIngress |
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:CreateCluster |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:DeleteCluster |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:DeregisterTaskDefinition |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:DescribeClusters |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:DescribeTaskDefinition |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:PutClusterCapacityProviders |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | ecs:RegisterTaskDefinition |
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:DeleteRule |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:DescribeRule |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:ListTagsForResource |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:ListTargetsByRule |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:PutRule |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:PutTargets |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | events:RemoveTargets |
| Scope | Permission |
|---|---|
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:CreateRole |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:DeleteRolePolicy |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:GetRole |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:GetRolePolicy |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:PutRolePolicy |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | iam:TagRole |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:CreateRole |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:DeleteRolePolicy |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:GetRole |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:GetRolePolicy |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:PutRolePolicy |
| <AWS_AWLS_MONITORED_ACCOUNT_ID> | iam:TagRole |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:CreatePolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:CreateRole |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:GetPolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:GetPolicyVersion |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:GetRole |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:GetRolePolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:PassRole |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:PutRolePolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | iam:TagRole |
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | logs:CreateLogGroup |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | logs:DeleteLogGroup |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | logs:DescribeLogGroups |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | logs:ListTagsLogGroup |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | logs:PutRetentionPolicy |
| Scope | Permission |
|---|---|
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | organizations:DescribeOrganization |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | organizations:ListAWSServiceAccessForOrganization |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | organizations:ListAccounts |
| <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | organizations:ListRoots |
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:CreateBucket |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:DeleteBucket* |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:Get* |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetAccelerateConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketAcl |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketCORS |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketLogging |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketObjectLockConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketOwnershipControls |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketPolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketPublicAccessBlock |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketRequestPayment |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketTagging |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketVersioning |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetBucketWebsite |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetEncryptionConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetLifecycleConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:GetReplicationConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:List* |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:ListBucket |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketAcl |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketLogging |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketNotification |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketOwnershipControls |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketPolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketPublicAccessBlock |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketTagging |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutBucketVersioning |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutEncryptionConfiguration |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | s3:PutLifecycleConfiguration |
| Scope | Permission |
|---|---|
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | secretsmanager:CreateSecret |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | secretsmanager:DescribeSecret |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | secretsmanager:GetResourcePolicy |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | secretsmanager:GetSecretValue |
| <AWS_AWLS_SCANNING_ACCOUNT_ID> | secretsmanager:PutSecretValue |
Permissions Used in Operation 📎
Agentless Workload Scanning
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-snapshot-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_MANAGEMENT_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::<AWS_AWLS_SCANNING_ACCOUNT_ID>:role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"LaceworkAgentlessWorkloadSnapshots",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"ec2:Describe*"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"DescribeInstances"
},
{
"Action":[
"ec2:CreateSnapshot"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshots"
},
{
"Action":[
"ec2:CreateTags"
],
"Condition":{
"StringEquals":{
"ec2:CreateAction":"CreateSnapshot"
}
},
"Effect":"Allow",
"Resource":[
"*"
],
"Sid":"CreateSnapshotTags"
},
{
"Action":[
"ec2:DeleteSnapshot",
"ec2:ModifySnapshotAttribute",
"ec2:ResetSnapshotAttribute",
"ebs:ListChangedBlocks",
"ebs:ListSnapshotBlocks",
"ebs:GetSnapshotBlock",
"ebs:CompleteSnapshot"
],
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotManagement"
},
{
"Action":[
"kms:DescribeKey",
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*"
],
"Condition":{
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryption"
},
{
"Action":[
"kms:CreateGrant"
],
"Condition":{
"Bool":{
"kms:GrantIsForAWSResource":"true"
},
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryptionGrants"
},
{
"Action":[
"organizations:Describe*",
"organizations:List*"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"OrgPermissions"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-snapshot-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_MONITORED_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::<AWS_AWLS_SCANNING_ACCOUNT_ID>:role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"LaceworkAgentlessWorkloadSnapshots",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"ec2:Describe*"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"DescribeInstances"
},
{
"Action":[
"ec2:CreateSnapshot"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshots"
},
{
"Action":[
"ec2:CreateTags"
],
"Condition":{
"StringEquals":{
"ec2:CreateAction":"CreateSnapshot"
}
},
"Effect":"Allow",
"Resource":[
"*"
],
"Sid":"CreateSnapshotTags"
},
{
"Action":[
"ec2:DeleteSnapshot",
"ec2:ModifySnapshotAttribute",
"ec2:ResetSnapshotAttribute",
"ebs:ListChangedBlocks",
"ebs:ListSnapshotBlocks",
"ebs:GetSnapshotBlock",
"ebs:CompleteSnapshot"
],
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotManagement"
},
{
"Action":[
"kms:DescribeKey",
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*"
],
"Condition":{
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryption"
},
{
"Action":[
"kms:CreateGrant"
],
"Condition":{
"Bool":{
"kms:GrantIsForAWSResource":"true"
},
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryptionGrants"
},
{
"Action":[
"organizations:Describe*",
"organizations:List*"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"OrgPermissions"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-cross-account-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_SCANNING_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"ECSTaskManagement",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"ecs:StopTask",
"ecs:RunTask"
],
"Condition":{
"ArnEquals":{
"ecs:cluster":"arn:aws:ecs:*:*:cluster\/lacework-agentless-scanning-cluster-<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Resource":[
"arn:aws:ecs:*:*:task\/lacework-agentless-scanning-cluster-<UNIQUE_ID>\/*",
"arn:aws:ecs:*:*:task-definition\/lacework-agentless-scanning-cluster-<UNIQUE_ID>:*"
],
"Sid":"AllowEcsStopTask"
},
{
"Action":"iam:PassRole",
"Effect":"Allow",
"Resource":[
"arn:aws:iam::*:role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>",
"arn:aws:iam::*:role\/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID>"
],
"Sid":"AllowEcsTaskManagementPassRole"
},
{
"Action":"ec2:DescribeSubnets",
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"arn:aws:ec2:*:*:subnet\/subnet-*",
"Sid":"AllowEcsTaskSubnetLookup"
}
]
}
},
{
"name":"S3WriteAllowPolicy",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"s3:PutBucketTagging",
"s3:ListBucket",
"s3:GetBucketTagging",
"s3:GetBucketLocation"
],
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>",
"Sid":"ListAndTagBucket"
},
{
"Action":[
"s3:PutObject",
"s3:GetObject",
"s3:DeleteObject"
],
"Effect":"Allow",
"Resource":"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>\/*",
"Sid":"PutGetDeleteObjectsInBucket"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/service-role\/lacework-agentless-scanning-task-event-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_SCANNING_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"events.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
"arn:aws:iam::aws:policy\/service-role\/AmazonEC2ContainerServiceEventsRole"
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_SCANNING_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"ecs-tasks.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
"arn:aws:iam::aws:policy\/service-role\/AmazonECSTaskExecutionRolePolicy",
{
"name":"AllowCloudWatch",
"policy":{
"Version":"2012-10-17",
"Statement":[
{
"Action":[
"logs:PutLogEvents",
"logs:CreateLogStream",
"logs:CreateLogGroup"
],
"Effect":"Allow",
"Resource":"arn:aws:logs:*:*:log-group:\/ecs\/lacework-agentless-scanning-*",
"Sid":"AllowLoggingToCloudWatch"
}
]
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lacework-agentless-scanning-task-role-<UNIQUE_ID>",
"Account":"<AWS_AWLS_SCANNING_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"ecs-tasks.amazonaws.com"
}
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lacework-agentless-scanning-task-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":"s3:*",
"Effect":"Allow",
"Resource":[
"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>\/*",
"arn:aws:s3:::lacework-agentless-scanning-bucket-<UNIQUE_ID>"
],
"Sid":"AllowControlOfBucket"
},
{
"Action":[
"ecs:UntagResource",
"ecs:TagResource",
"ecs:ListTagsForResource"
],
"Condition":{
"StringLike":{
"ecs:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"AllowTagECSCluster"
},
{
"Action":[
"events:ListTargetsByRule",
"events:ListTagsForResource",
"events:ListRules",
"events:ListRuleNamesByTarget",
"events:DescribeRule"
],
"Effect":"Allow",
"Resource":"*",
"Sid":"AllowListRules"
},
{
"Action":[
"events:RemoveTargets",
"events:PutTargets",
"events:EnableRule",
"events:DisableRule"
],
"Effect":"Allow",
"Resource":"arn:aws:events:*:*:rule\/lacework-agentless-scanning-periodic-trigger-<UNIQUE_ID>",
"Sid":"AllowUpdateRule"
},
{
"Action":[
"secretsmanager:ListSecretVersionIds",
"secretsmanager:GetSecretValue",
"secretsmanager:GetResourcePolicy"
],
"Effect":"Allow",
"Resource":"arn:aws:secretsmanager:us-east-1:<AWS_AWLS_SCANNING_ACCOUNT_ID>:secret:lacework-agentless-scanning-secret-<UNIQUE_ID>",
"Sid":"AllowReadFromSecretsManager"
},
{
"Action":"ec2:Describe*",
"Effect":"Allow",
"Resource":"*",
"Sid":"DescribeInstances"
},
{
"Action":"ec2:CreateSnapshot",
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshots"
},
{
"Action":"ec2:CreateTags",
"Condition":{
"StringEquals":{
"ec2:CreateAction":"CreateSnapshot"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"CreateSnapshotTags"
},
{
"Action":[
"ec2:ResetSnapshotAttribute",
"ec2:ModifySnapshotAttribute",
"ec2:DeleteSnapshot",
"ebs:ListSnapshotBlocks",
"ebs:ListChangedBlocks",
"ebs:GetSnapshotBlock",
"ebs:CompleteSnapshot"
],
"Condition":{
"StringLike":{
"aws:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotManagement"
},
{
"Action":[
"ecs:StopTask",
"ecs:StartTask",
"ecs:RunTask",
"ecs:ListTasks",
"ecs:Describe*"
],
"Condition":{
"ArnEquals":{
"ecs:cluster":"arn:aws:ecs:*:*:cluster\/lacework-agentless-scanning-cluster-<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"TaskManagement"
},
{
"Action":[
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:Encrypt",
"kms:DescribeKey",
"kms:Decrypt"
],
"Condition":{
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryption"
},
{
"Action":"kms:CreateGrant",
"Condition":{
"Bool":{
"kms:GrantIsForAWSResource":"true"
},
"StringLike":{
"kms:ViaService":"ec2.*.amazonaws.com"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"SnapshotEncryptionGrants"
},
{
"Action":[
"sts:AssumeRole",
"iam:PassRole"
],
"Condition":{
"StringLike":{
"iam:ResourceTag\/LWTAG_SIDEKICK":"*"
}
},
"Effect":"Allow",
"Resource":"*",
"Sid":"PassRoleToTasks"
},
{
"Action":"sts:DecodeAuthorizationMessage",
"Effect":"Allow",
"Resource":"*",
"Sid":"DecodeErrorMessages"
},
{
"Action":[
"logs:GetLogEvents",
"logs:DescribeLogStreams"
],
"Effect":"Allow",
"Resource":"arn:aws:logs:*:*:log-group:\/ecs\/lacework-agentless-scanning-*",
"Sid":"ReadLogs"
}
],
"Version":"2012-10-17"
}
}
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lacework-agentless-scanning-snapshot-role-<UNIQUE_ID> | <AWS_AWLS_MANAGEMENT_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-snapshot-role-<UNIQUE_ID> | <AWS_AWLS_MONITORED_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-cross-account-role-<UNIQUE_ID> | <AWS_AWLS_SCANNING_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/service-role/lacework-agentless-scanning-task-event-role-<UNIQUE_ID> | <AWS_AWLS_SCANNING_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-task-execution-role-<UNIQUE_ID> | <AWS_AWLS_SCANNING_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lacework-agentless-scanning-task-role-<UNIQUE_ID> | <AWS_AWLS_SCANNING_ACCOUNT_ID> | { | [ |
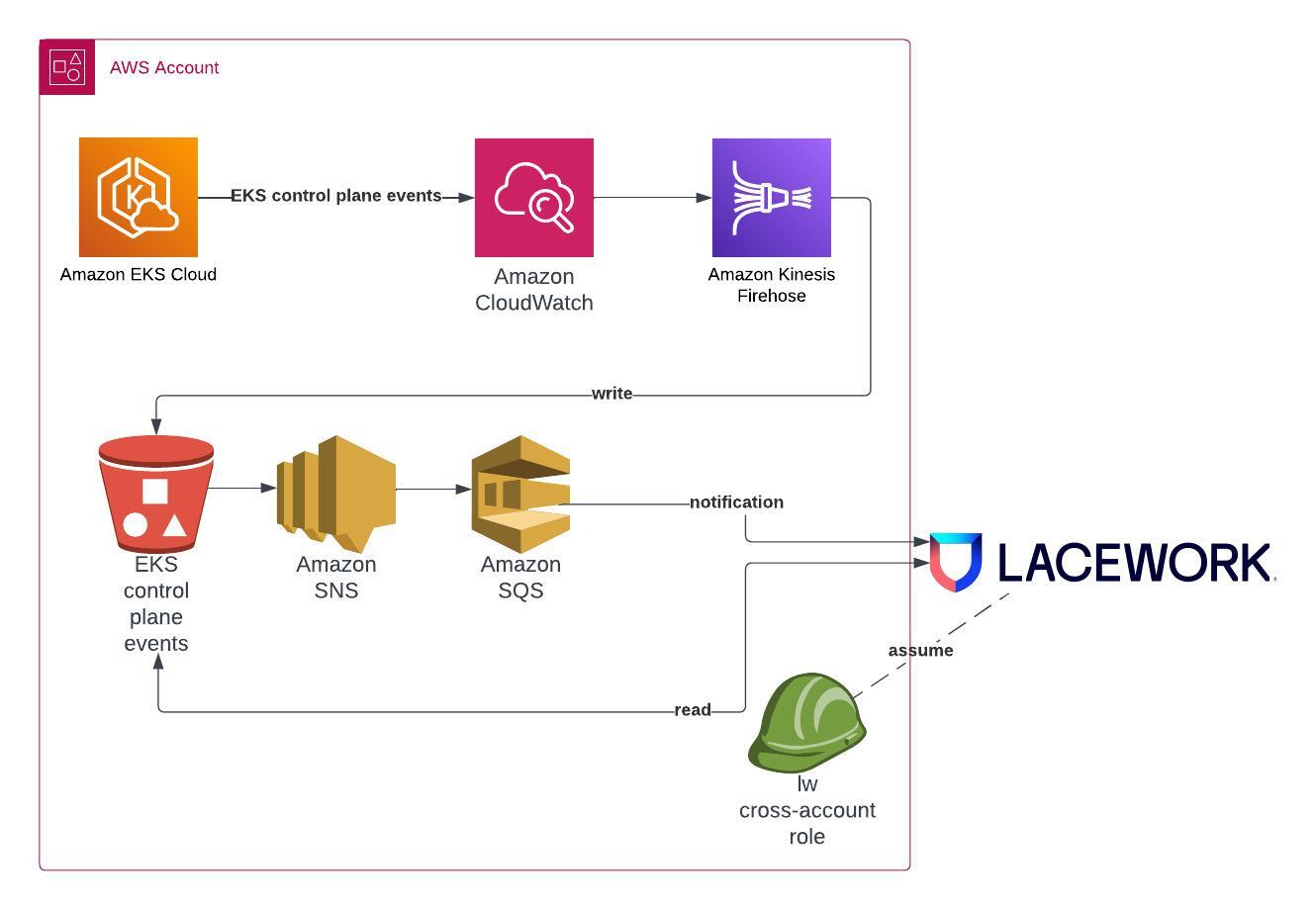
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| User Entity Behaviour Analytics (UEBA) | Kubernetes Audit Log Dashboard Kubernetes Anomaly Detection Kubernetes Audit Log Polygraph | EKS Audit |
Prerequisites 📎
Overview
Lacework integrates with AWS to analyze EKS Audit Logs for monitoring EKS cluster security and configuration compliance. This topic describes how to integrate with AWS by running Lacework Terraform modules from any host supported by Terraform.
If you are new to the Lacework Terraform provider, or Lacework Terraform modules, read Terraform for Lacework Overview to learn the basics on how to configure the provider and more.
Resources Provisioned by Lacework Terraform Modules
To integrate AWS with Lacework, Lacework Terraform modules provision the following resources in the designated AWS account:
- IAM Cross-Account Role - A cross-account role is required to give access to Lacework access for assessments of cloud resource configurations and for analysis of CloudTrail events. The cross-account role will be given the following policy:
- Lacework Custom IAM Policy - A custom policy that provides Lacework read-only access to ingest EKS Audit Logs.
- SNS Topic - An SNS topic is required for all EKS Audit Log integrations. Terraform will create a new topic in the designated account.
- S3 Bucket - An S3 bucket is required for all EKS Audit Log integrations. Lacework will create a new bucket in the designated account.
- S3 Bucket Notification - A S3 Bucket notification is required for all EKS Audit Log integrations. This notifies the SNS topic when a new object has been created in the bucket.
- S3 Bucket Lifecycle rule - An S3 Bucket Lifecycle rule to specify the log number of days the logs are retained. Defaults to 180 days.
- S3 Bucket versioning - A resource for controlling versioning on an S3 bucket.
- Kinesis Firehose - A Kinesis Firehose is required for all EKS Audit Log integrations. Lacework will create a new Firehose in the designated account.
- IAM Lacework Firehose Role - A firehose role is required to assume the AWS firehose service role.
- Lacework Firehose IAM Policy - A firehose policy is required to allow the firehose to manage the contents of the S3 bucket.
- IAM Lacework CloudWatch Role - A CloudWatch role is required to assume the logs role for each region integrated.
- Lacework CloudWatch IAM Policy - A CloudWatch policy is required to allow the firehose to access the CloudWatch logs.
- CloudWatch Subscription Filter(s) - CloudWatch subscription filter(s) are required for each EKS cluster in order to notify when logs have been added to the CloudWatch Log group.
Requirements
- AWS Account Admin - The account used to run Terraform must have administrative privileges on every AWS account you intend to integrate with Lacework.
- AWS CLI - The Terraform provider for AWS leverages the configuration from the AWS CLI and it is recommended the AWS CLI is installed and configured with API keys for the account being integrated.
- Lacework Administrator - A Lacework account with administrator privileges.
- Lacework CLI - Lacework leverages the configuration from the Lacework CLI. Installing and configuring the Lacework CLI is recommended.
- Terraform -
~> 0.15,~> 1.0,~> 1.1.
Module Inputs Reference
For an up-to-date guide on all available configuration inputs, refer to the Terraform Registry documentation:
Module Dependencies
Lacework Terraform modules for AWS have the following dependencies that are installed when running terraform init:
For detailed information on these dependencies, visit Lacework on the Terraform Registry.
Architecture 📎
Permissions Required for Deployment 📎
EKS Audit
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"firehose:CreateDeliveryStream",
"firehose:DeleteDeliveryStream",
"firehose:DescribeDeliveryStream",
"firehose:ListTagsForDeliveryStream",
"firehose:StartDeliveryStreamEncryption",
"iam:AttachRolePolicy",
"iam:CreatePolicy",
"iam:CreateRole",
"iam:DeletePolicy",
"iam:DeleteRole",
"iam:DetachRolePolicy",
"iam:GetPolicy",
"iam:GetPolicyVersion",
"iam:GetRole",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListPolicyVersions",
"iam:ListRolePolicies",
"iam:PassRole",
"iam:TagRole",
"kms:CancelKeyDeletion",
"kms:Create*",
"kms:CreateAlias",
"kms:CreateKey",
"kms:Delete*",
"kms:DeleteAlias",
"kms:Describe*",
"kms:DescribeKey",
"kms:Disable*",
"kms:Enable*",
"kms:EnableKeyRotation",
"kms:Get*",
"kms:GetKeyPolicy",
"kms:GetKeyRotationStatus",
"kms:List*",
"kms:ListAliases",
"kms:ListResourceTags",
"kms:Put*",
"kms:Revoke*",
"kms:ScheduleKeyDeletion",
"kms:TagResource",
"kms:Update*",
"logs:DeleteSubscriptionFilter",
"logs:DescribeSubscriptionFilters",
"logs:PutSubscriptionFilter",
"s3:CreateBucket",
"s3:DeleteBucket",
"s3:DeleteBucket*",
"s3:Get*",
"s3:GetAccelerateConfiguration",
"s3:GetBucketAcl",
"s3:GetBucketCORS",
"s3:GetBucketLogging",
"s3:GetBucketNotification",
"s3:GetBucketObjectLockConfiguration",
"s3:GetBucketOwnershipControls",
"s3:GetBucketPolicy",
"s3:GetBucketPublicAccessBlock",
"s3:GetBucketRequestPayment",
"s3:GetBucketTagging",
"s3:GetBucketVersioning",
"s3:GetBucketWebsite",
"s3:GetEncryptionConfiguration",
"s3:GetLifecycleConfiguration",
"s3:GetReplicationConfiguration",
"s3:List*",
"s3:ListBucket",
"s3:PutBucketAcl",
"s3:PutBucketLogging",
"s3:PutBucketNotification",
"s3:PutBucketOwnershipControls",
"s3:PutBucketPolicy",
"s3:PutBucketPublicAccessBlock",
"s3:PutBucketVersioning",
"s3:PutEncryptionConfiguration",
"s3:PutLifecycleConfiguration",
"sns:CreateTopic",
"sns:DeleteTopic",
"sns:GetTopicAttributes",
"sns:ListTagsForResource",
"sns:SetTopicAttributes"
],
"Resource": "*"
}
]
}
- Kinesis Firehose
- IAM
- KMS
- Logs
- S3
- SNS
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | firehose:CreateDeliveryStream |
| <AWS_ACCOUNT_ID> | firehose:DeleteDeliveryStream |
| <AWS_ACCOUNT_ID> | firehose:DescribeDeliveryStream |
| <AWS_ACCOUNT_ID> | firehose:ListTagsForDeliveryStream |
| <AWS_ACCOUNT_ID> | firehose:StartDeliveryStreamEncryption |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:CreatePolicy |
| <AWS_ACCOUNT_ID> | iam:CreateRole |
| <AWS_ACCOUNT_ID> | iam:DeletePolicy |
| <AWS_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_ACCOUNT_ID> | iam:DetachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicy |
| <AWS_ACCOUNT_ID> | iam:GetPolicyVersion |
| <AWS_ACCOUNT_ID> | iam:GetRole |
| <AWS_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_ACCOUNT_ID> | iam:ListPolicyVersions |
| <AWS_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_ACCOUNT_ID> | iam:PassRole |
| <AWS_ACCOUNT_ID> | iam:TagRole |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | kms:CancelKeyDeletion |
| <AWS_ACCOUNT_ID> | kms:Create* |
| <AWS_ACCOUNT_ID> | kms:CreateAlias |
| <AWS_ACCOUNT_ID> | kms:CreateKey |
| <AWS_ACCOUNT_ID> | kms:Delete* |
| <AWS_ACCOUNT_ID> | kms:DeleteAlias |
| <AWS_ACCOUNT_ID> | kms:Describe* |
| <AWS_ACCOUNT_ID> | kms:DescribeKey |
| <AWS_ACCOUNT_ID> | kms:Disable* |
| <AWS_ACCOUNT_ID> | kms:Enable* |
| <AWS_ACCOUNT_ID> | kms:EnableKeyRotation |
| <AWS_ACCOUNT_ID> | kms:Get* |
| <AWS_ACCOUNT_ID> | kms:GetKeyPolicy |
| <AWS_ACCOUNT_ID> | kms:GetKeyRotationStatus |
| <AWS_ACCOUNT_ID> | kms:List* |
| <AWS_ACCOUNT_ID> | kms:ListAliases |
| <AWS_ACCOUNT_ID> | kms:ListResourceTags |
| <AWS_ACCOUNT_ID> | kms:Put* |
| <AWS_ACCOUNT_ID> | kms:Revoke* |
| <AWS_ACCOUNT_ID> | kms:ScheduleKeyDeletion |
| <AWS_ACCOUNT_ID> | kms:TagResource |
| <AWS_ACCOUNT_ID> | kms:Update* |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | logs:DeleteSubscriptionFilter |
| <AWS_ACCOUNT_ID> | logs:DescribeSubscriptionFilters |
| <AWS_ACCOUNT_ID> | logs:PutSubscriptionFilter |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | s3:CreateBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket |
| <AWS_ACCOUNT_ID> | s3:DeleteBucket* |
| <AWS_ACCOUNT_ID> | s3:Get* |
| <AWS_ACCOUNT_ID> | s3:GetAccelerateConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketAcl |
| <AWS_ACCOUNT_ID> | s3:GetBucketCORS |
| <AWS_ACCOUNT_ID> | s3:GetBucketLogging |
| <AWS_ACCOUNT_ID> | s3:GetBucketNotification |
| <AWS_ACCOUNT_ID> | s3:GetBucketObjectLockConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:GetBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:GetBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:GetBucketRequestPayment |
| <AWS_ACCOUNT_ID> | s3:GetBucketTagging |
| <AWS_ACCOUNT_ID> | s3:GetBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:GetBucketWebsite |
| <AWS_ACCOUNT_ID> | s3:GetEncryptionConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetLifecycleConfiguration |
| <AWS_ACCOUNT_ID> | s3:GetReplicationConfiguration |
| <AWS_ACCOUNT_ID> | s3:List* |
| <AWS_ACCOUNT_ID> | s3:ListBucket |
| <AWS_ACCOUNT_ID> | s3:PutBucketAcl |
| <AWS_ACCOUNT_ID> | s3:PutBucketLogging |
| <AWS_ACCOUNT_ID> | s3:PutBucketNotification |
| <AWS_ACCOUNT_ID> | s3:PutBucketOwnershipControls |
| <AWS_ACCOUNT_ID> | s3:PutBucketPolicy |
| <AWS_ACCOUNT_ID> | s3:PutBucketPublicAccessBlock |
| <AWS_ACCOUNT_ID> | s3:PutBucketVersioning |
| <AWS_ACCOUNT_ID> | s3:PutEncryptionConfiguration |
| <AWS_ACCOUNT_ID> | s3:PutLifecycleConfiguration |
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | sns:CreateTopic |
| <AWS_ACCOUNT_ID> | sns:DeleteTopic |
| <AWS_ACCOUNT_ID> | sns:GetTopicAttributes |
| <AWS_ACCOUNT_ID> | sns:ListTagsForResource |
| <AWS_ACCOUNT_ID> | sns:SetTopicAttributes |
Permissions Used in Operation 📎
Agentless Workload Scanning
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lw-eks-al-cw-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"logs.us-east-1.amazonaws.com"
},
"Sid":"LaceworkEKSCloudWatchIAMRole"
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lw-eks-al-cw-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":[
"firehose:PutRecordBatch",
"firehose:PutRecord"
],
"Effect":"Allow",
"Resource":"arn:aws:firehose:*:<AWS_ACCOUNT_ID>:deliverystream\/lw-eks-al<UNIQUE_ID>",
"Sid":""
}
],
"Version":"2012-10-17"
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lw-eks-al-fh-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Effect":"Allow",
"Principal":{
"Service":"firehose.amazonaws.com"
},
"Sid":"LaceworkEKSFirehoseIAMRole"
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lw-eks-al-fh-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":[
"s3:PutObject",
"s3:ListBucketMultipartUploads",
"s3:ListBucket",
"s3:GetObject",
"s3:GetBucketLocation",
"s3:AbortMultipartUpload"
],
"Effect":"Allow",
"Resource":"arn:aws:s3:::lw-eks-al<UNIQUE_ID>\/*",
"Sid":"LaceworkEKSFirehoseIAMRole"
}
],
"Version":"2012-10-17"
}
}
]
},
{
"Type":"aws_iam_role",
"Name":"role\/lw-eks-al-ca-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
{
"name":"lw-eks-al-cross-acct-policy-<UNIQUE_ID>",
"policy":{
"Statement":[
{
"Action":[
"s3:ListObjectsV2",
"s3:ListBucket",
"s3:Get*"
],
"Effect":"Allow",
"Resource":[
"arn:aws:s3:::lw-eks-al<UNIQUE_ID>\/*",
"arn:aws:s3:::lw-eks-al<UNIQUE_ID>"
],
"Sid":"S3Permissions"
},
{
"Action":[
"logs:PutSubscriptionFilter",
"logs:DescribeSubscriptionFilters"
],
"Effect":"Allow",
"Resource":"arn:aws:logs:*:<AWS_ACCOUNT_ID>:log-group:\/aws\/eks\/*:*",
"Sid":"CloudWatchLogsPermissions"
},
{
"Action":[
"iam:PassRole",
"iam:GetRole"
],
"Effect":"Allow",
"Resource":"arn:aws:iam::<AWS_ACCOUNT_ID>:role\/*lw-eks-al-eks-cw*",
"Sid":"IAMPermissions"
},
{
"Action":[
"sns:Unsubscribe",
"sns:Subscribe",
"sns:GetTopicAttributes"
],
"Effect":"Allow",
"Resource":"arn:aws:sns:us-east-1:<AWS_ACCOUNT_ID>:lw-eks-al<UNIQUE_ID>",
"Sid":"SNSPermissions"
},
{
"Action":"firehose:DescribeDeliveryStream",
"Effect":"Allow",
"Resource":"arn:aws:firehose:us-east-1:<AWS_ACCOUNT_ID>:deliverystream\/lw-eks-al<UNIQUE_ID>",
"Sid":"FirehosePermissions"
},
{
"Action":"iam:ListAccountAliases",
"Effect":"Allow",
"Resource":"*",
"Sid":"AccountAliasPermissions"
}
],
"Version":"2012-10-17"
}
}
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lw-eks-al-cw-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lw-eks-al-fh-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| aws_iam_role | role/lw-eks-al-ca-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | ECR |
Prerequisites 📎
Container Registry Support
Amazon Elastic Container Registry (ECR) integrations support:
- Auto polling - polling occurs every 15 minutes.
- On-demand scans via the API.
Amazon ECR's integration maximum is 1000 repositories due to set limitations with the Docker V2 APIs.
Lacework scans the latest 5 tags per image in an ECR repository.
Architecture 📎
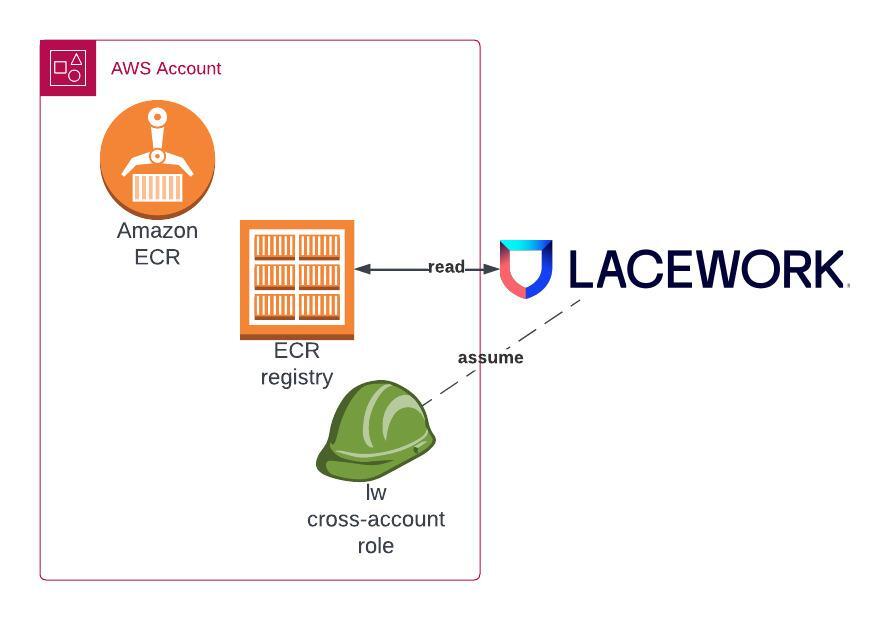
Permissions Required for Deployment 📎
ECR
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:View JSON 📎
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"iam:AttachRolePolicy",
"iam:CreateRole",
"iam:DeleteRole",
"iam:DetachRolePolicy",
"iam:GetRole",
"iam:ListAttachedRolePolicies",
"iam:ListInstanceProfilesForRole",
"iam:ListRolePolicies",
"iam:TagRole"
],
"Resource": "*"
}
]
}
- IAM
| Scope | Permission |
|---|---|
| <AWS_ACCOUNT_ID> | iam:AttachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:CreateRole |
| <AWS_ACCOUNT_ID> | iam:DeleteRole |
| <AWS_ACCOUNT_ID> | iam:DetachRolePolicy |
| <AWS_ACCOUNT_ID> | iam:GetRole |
| <AWS_ACCOUNT_ID> | iam:ListAttachedRolePolicies |
| <AWS_ACCOUNT_ID> | iam:ListInstanceProfilesForRole |
| <AWS_ACCOUNT_ID> | iam:ListRolePolicies |
| <AWS_ACCOUNT_ID> | iam:TagRole |
Permissions Used in Operation 📎
ECR
View JSON 📎
[
{
"Type":"aws_iam_role",
"Name":"role\/lw-iam-<UNIQUE_ID>",
"Account":"<AWS_ACCOUNT_ID>",
"Trust Relationships":{
"Statement":[
{
"Action":"sts:AssumeRole",
"Condition":{
"StringEquals":{
"sts:ExternalId":"lweid:aws:v2:<ACCOUNT>:<AWS_ACCOUNT_ID>:<UNIQUE_ID>"
}
},
"Effect":"Allow",
"Principal":{
"AWS":"arn:aws:iam::434813966438:root"
},
"Sid":""
}
],
"Version":"2012-10-17"
},
"Permissions":[
"arn:aws:iam::aws:policy\/AmazonEC2ContainerRegistryReadOnly"
]
}
]
| Type | Name | Account | Trust Relationships | Permissions |
|---|---|---|---|---|
| aws_iam_role | role/lw-iam-<UNIQUE_ID> | <AWS_ACCOUNT_ID> | { | [ |