Azure
Cloud Security and Compliance provides supports the following Use Cases and Lacework Features:
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | Azure Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | Azure Cloud Audit Logs |
| Vulnerability Management | Vulnerability Management Dashboard | ACR |
See below for information on planning Lacework integrations and the specific use cases for each integration:
- Cloud Audit and Configuration
- ACR
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | Azure Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | Azure Cloud Audit Logs |
Prerequisites 📎
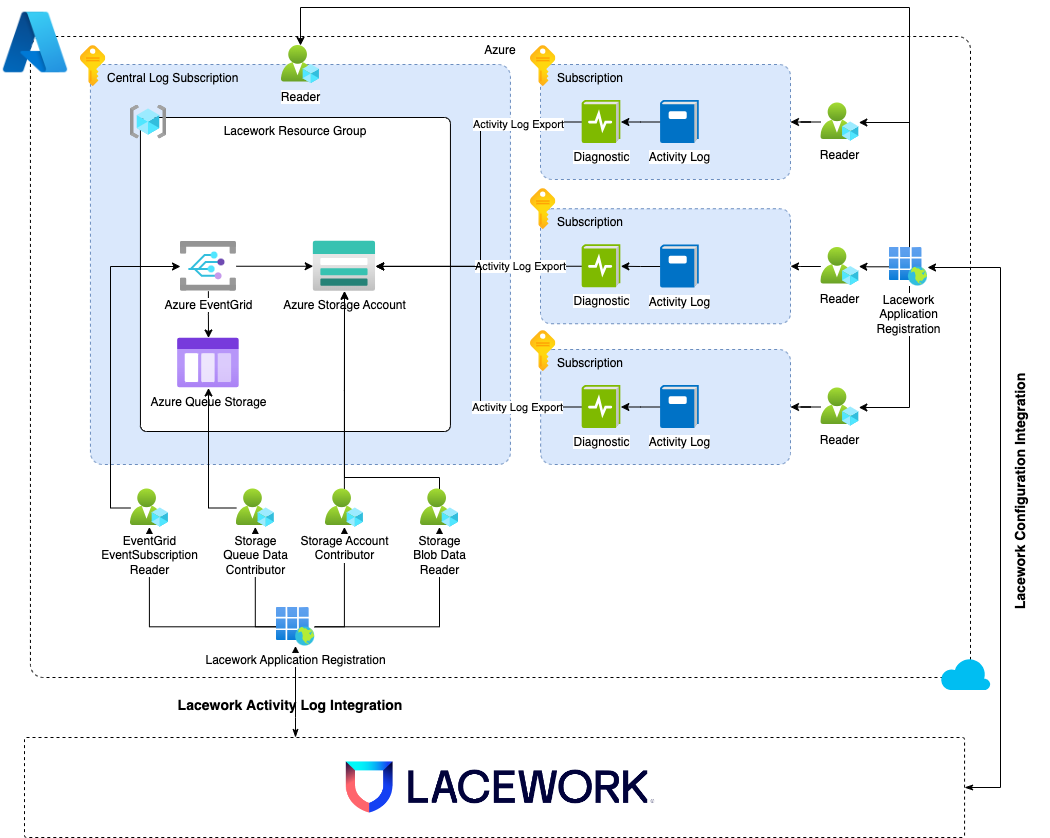
Architecture 📎
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | ACR |