Google Cloud
Cloud Security and Compliance provides supports the following Use Cases and Lacework Features:
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | Google Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | Google Cloud Audit Logs |
| Vulnerability Management | Vulnerability Management Dashboard | GCR GAR Agentless Workload Scanning |
| User Entity Behaviour Analytics (UEBA) | Kubernetes Audit Log Dashboard Kubernetes Anomaly Detection Kubernetes Audit Log Polygraph | GKE Audit |
See below for information on planning Lacework integrations and the specific use cases for each integration:
- Cloud Audit and Configuration
- Agentless Workload Scanning
- GKE Audit
- GCR
- GAR
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Cloud Security Posture Management (CSPM) Cloud Infrastructure Entitilement Management (CIEM) | Compliance Dashboard and Reports Cloud Infrastructure Entitilement Management Dashboard Attack Path Analysis and Exposure Polygraph | Google Cloud Configuration |
| User Entity Behaviour Analytics (UEBA) | Cloud Anomaly Detection Cloud Drift Detection Cloud Audit Polygraph | Google Cloud Audit Logs |
Prerequisites 📎
Ingested Logs
Lacework ingests Admin Activity logs and Data Access logs. Admin Activity logs are enabled by GCP by default. You may have to enable Data Access logs at an additional cost from GCP to access the following event groups:
- ADMIN_READ: access to Kubernetes metadata and configuration
- DATA_READ: access to Kubernetes resources
- DATA_WRITE: creation and changes to Kubernetes resources
Required Google Cloud APIs 📎
When you manually create a GCP Configuration or Audit Log integration, it is important to enable the required APIs in the correct way for the integration to work as expected.
API List
Use this table as a reference when enabling the APIs in the How to Enable the APIs section below.
Lacework recommends that all the APIs listed below are enabled on the project that hosts the service account.
If they are not enabled, Lacework is not able to assess other projects that have these APIs enabled (or if they are enabled in the future).
| API Name | API URL | Integration Type |
|---|---|---|
| Cloud Resource Manager API | cloudresourcemanager.googleapis.com | Audit Log Configuration |
| Identity and Access Management (IAM) API | iam.googleapis.com | Audit Log Configuration |
| Service Usage API | serviceusage.googleapis.com | Audit Log Configuration |
| BigQuery API | bigquery.googleapis.com | Configuration |
| Cloud Asset API | cloudasset.googleapis.com | Configuration |
| Cloud DNS API | dns.googleapis.com | Configuration |
| Cloud Key Management Service (KMS) API | cloudkms.googleapis.com | Configuration |
| Cloud Logging API | logging.googleapis.com | Configuration |
| Cloud Pub/Sub API | pubsub.googleapis.com | Audit Log Configuration |
| Cloud SQL Admin API | sqladmin.googleapis.com | Configuration |
| Cloud Storage | storage-component.googleapis.com | Configuration |
| Compute Engine API | compute.googleapis.com | Configuration |
| Essential Contact API | essentialcontacts.googleapis.com | Configuration |
| Kubernetes Engine API | container.googleapis.com | Configuration |
How to Enable the APIs
For the project that hosts the service account for the integration, enable each of the APIs listed in the API List by choosing one of the methods below.
Enable using the GCP Console
Log in to the GCP Console and click
.
Select APIs & Services > Library.
In the Search for APIs & Services field, enter the API URL listed in the table above such as iam.googleapis.com.
Click on the result that matches the API name listed above, such as Identity and Access Management (IAM) API.
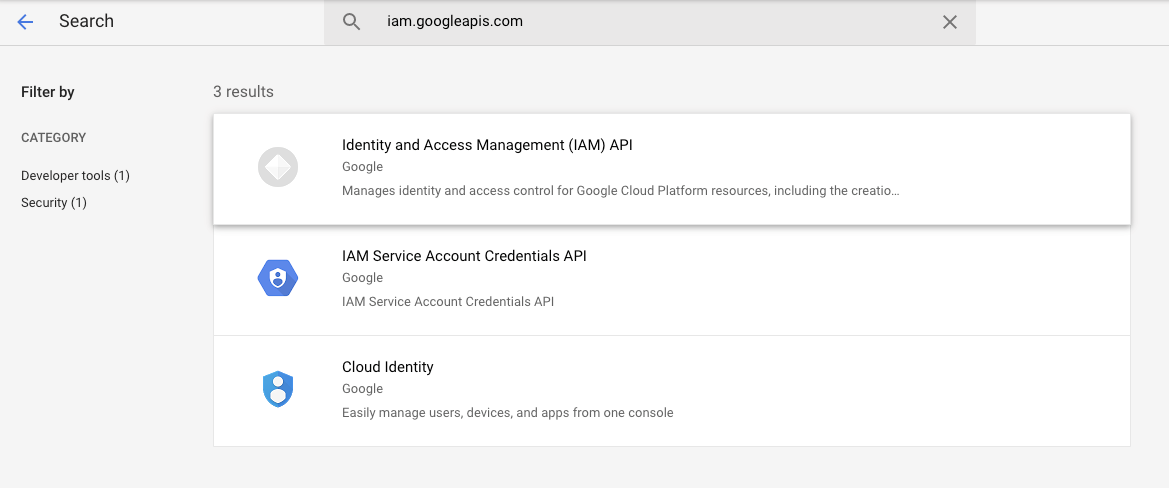
Click Enable.
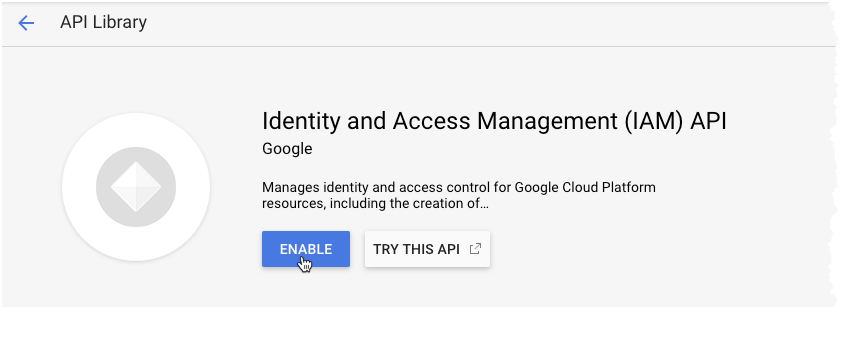
If you are prompted to enable billing, click Enable Billing.
Repeat these steps for each GCP project that hosts a service account that you are using for your Lacework integration.
Enable using the gcloud CLI
Ensure that the gcloud config is set to use a service account with the permissions required to enable APIs.
For further information about enabling APIs, see the Google Cloud documentation.
Set the project that you wish to enable the APIs on:
gcloud config set project target_projectEnable the required APIs for your integration type:
Configuration Integrationgcloud services enable \
cloudresourcemanager.googleapis.com \
iam.googleapis.com \
serviceusage.googleapis.com \
bigquery.googleapis.com \
cloudasset.googleapis.com \
dns.googleapis.com \
cloudkms.googleapis.com \
logging.googleapis.com \
pubsub.googleapis.com \
sqladmin.googleapis.com \
storage-component.googleapis.com \
compute.googleapis.com \
essentialcontacts.googleapis.com \
container.googleapis.comPub/Sub-Based Audit Log Integrationgcloud services enable \
pubsub.googleapis.com \
cloudresourcemanager.googleapis.com \
iam.googleapis.com \
serviceusage.googleapis.comStorage-Based Audit Log Integrationgcloud services enable \
pubsub.googleapis.com \
cloudresourcemanager.googleapis.com \
iam.googleapis.com \
serviceusage.googleapis.comVerify the APIs were successfully enabled:
gcloud services list
Architecture 📎
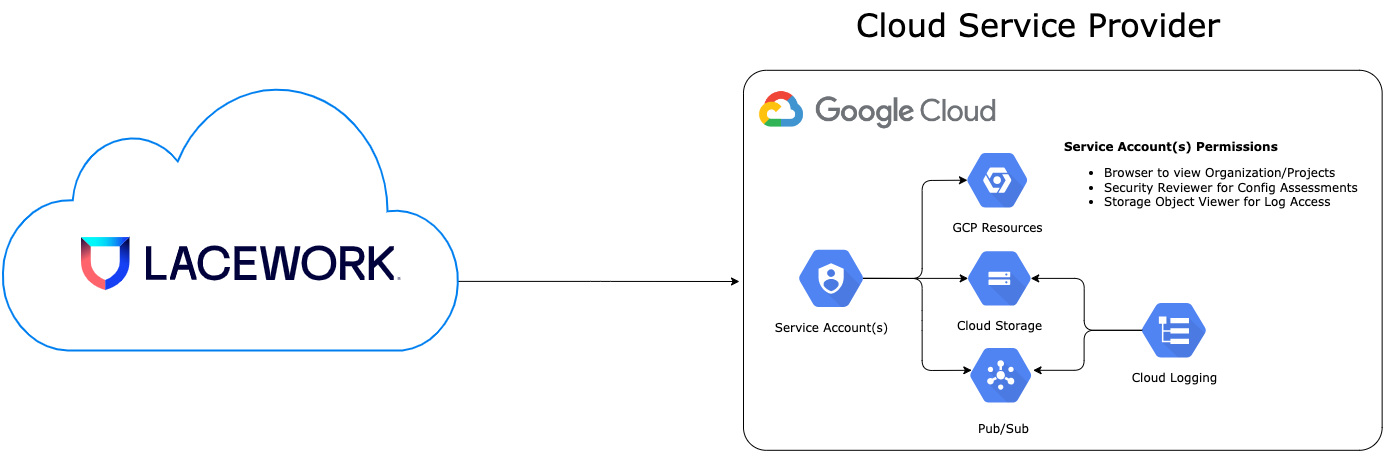
Single Project Integration
Permissions Required for Deployment 📎
Cloud Audit and Config
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.undelete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.attachSubscription |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.objects.delete |
Permissions Used in Operation 📎
Cloud Audit and Config
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-at-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-at-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-cfg-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-cfg-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lwComplianceRole_<UNIQUE_ID> | Lacework Compliance Role | [ |
Single Project Integration (Pubsub)
Permissions Required for Deployment 📎
Cloud Audit and Config (Pubsub Integration Type)
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.undelete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.attachSubscription |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
Permissions Used in Operation 📎
Cloud Audit and Config (Pubsub Integration Type)
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-cfg-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-cfg-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-al-ps-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-al-ps-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lwComplianceRole_<UNIQUE_ID> | Lacework Compliance Role | [ |
Organization Level Integration
Permissions Required for Deployment 📎
Cloud Audit and Config (Org Integration)
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | compute.projects.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.create |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.delete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.list |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.undelete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.update |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.create |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.delete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.list |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.getIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.setIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.quotas.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.attachSubscription |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.objects.delete |
Permissions Used in Operation 📎
Cloud Audit and Config (Org Integration)
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-at-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-at-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-cfg-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-cfg-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_organization_iam_custom_role | organizations/<GCP_ORG_ACCOUNT>/roles/lwOrgComplianceRole_<UNIQUE_ID> | Lacework Org Compliance Role | [ |
Organization Level Integration (PubSub)
Permissions Required for Deployment 📎
Cloud Audit and Config (Pubsub and Org Integration Type)
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | compute.projects.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.create |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.delete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.list |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.undelete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.update |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.create |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.delete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | logging.sinks.list |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.getIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.setIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.quotas.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.attachSubscription |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
Permissions Used in Operation 📎
Cloud Audit and Config (Pubsub and Org Integration Type)
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-cfg-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-cfg-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-al-ps-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-al-ps-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_organization_iam_custom_role | organizations/<GCP_ORG_ACCOUNT>/roles/lwOrgComplianceRole_<UNIQUE_ID> | Lacework Org Compliance Role | [ |
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | Agentless Workload Scanning |
Prerequisites 📎
Overview
This article explains the requirements for an Agentless Workload Scanning integration using Terraform.
Once you have read and completed the Prerequisites, complete the integration steps depending on your chosen integration level:
- Project Integration (Single or Multi Region)
- Organization Integration (Single or Multi Region)
If you want to specify a custom VPC network/subnetwork for your integration, see the section linked below for an example:
The Agentless Workload Scanning integration is configured with Terraform using the lacework_gcp_agentless_scanning module.
If you are new to the Lacework Terraform Provider, or Lacework Terraform Modules, read Terraform for Lacework Overview to learn the basics on how to configure the provider.
This module will install global and regional resources. The global resources should be installed once for a Lacework integration. The regional resources should be installed in each region where scanning will occur. Having per-region resources assures that no cross-region traffic occurs.
Custom VPC Network/Subnetwork for Google Cloud Terraform Integrations
Follow the example below if you want to specify a custom network/subnetwork for your Google Cloud integration.
In this example, we add Terraform modules to two Google Cloud regions for a project level integration (similar to Option 2: Project Integration - Multi Region):
- Global resources are deployed to
us-east1.- Service Accounts/Permissions
- Object Storage Bucket
- Secret Manager Secret
- Custom VPC Network
- Firewall Rules for Agentless Workload Scanning
- Regional resources are deployed to
us-east1andus-central1.- Cloud Run Job
- Cloud Scheduler Job
- Custom VPC Subnetwork
-
Use the example below for your
versions.tffile:terraform { required_version = ">= 0.12.31" required_providers { lacework = { source = "lacework/lacework" } } } -
Use the example below for your
main.tffile:# Set your Lacework profile here. With the Lacework CLI, use # `lacework configure list` to get a list of available profiles. provider "lacework" { profile = "lw_agentless" } provider "google" { alias = "use1" region = "us-east1" # Set the project name for where the scanning resources are hosted. # This must be assigned to the `global` region. project = "agentless-lw-scanner" } provider "google" { alias = "usc1" region = "us-central1" # Set your default project ID for this region. This isn't required for # the Agentless integration, but is required by the Google Provider. # https://registry.terraform.io/providers/hashicorp/google/latest/docs/guides/getting_started#configuring-the-provider project = "default-project-id" } locals { # Provide a list of Google Cloud projects that you want to monitor here. project_filter_list = [ "monitored-project-1", "monitored-project-2" ] } resource "google_compute_network" "awls" { provider = google.use1 name = "lacework-awls" auto_create_subnetworks = false } resource "google_compute_subnetwork" "awls_subnet_1" { provider = google.use1 name = "lacework-awls-subnet1" ip_cidr_range = "10.10.1.0/24" network = google_compute_network.awls.id } resource "google_compute_subnetwork" "awls_subnet_2" { provider = google.usc1 name = "lacework-awls-subnet2" ip_cidr_range = "10.10.2.0/24" network = google_compute_network.awls.id } resource "google_compute_firewall" "rules" { provider = google.use1 name = "awls-allow-https-egress" network = google_compute_network.awls.name description = "Firewall policy for Lacework Agentless Workload Scanning" direction = "EGRESS" destination_ranges = [ "0.0.0.0/0" ] allow { protocol = "tcp" ports = ["443"] } } module "lacework_gcp_agentless_scanning_project_multi_region_use1" { source = "lacework/agentless-scanning/gcp" version = "~> 0.1" providers = { google = google.use1 } project_filter_list = local.project_filter_list global = true regional = true custom_vpc_subnet = google_compute_subnetwork.awls_subnet_1.id } module "lacework_gcp_agentless_scanning_project_multi_region_usc1" { source = "lacework/agentless-scanning/gcp" version = "~> 0.1" providers = { google = google.usc1 } project_filter_list = local.project_filter_list regional = true global_module_reference = module.lacework_gcp_agentless_scanning_project_multi_region_use1 custom_vpc_subnet = google_compute_subnetwork.awls_subnet_2.id } -
If you are executing Terraform outside the Google Cloud Console, use the following gcloud commands prior to running Terraform:
-
gcloud auth login -
gcloud auth application-default login -
gcloud config set project <scanning_project>- Replace
<scanning-project>with the project that will host the scanning resources (agentless-lw-scannerin this example).
- Replace
-
-
Run
terraform initto initialize the working directory (containing the Terraform files). -
Run
terraform planand review the changes that will be applied. -
Once satisfied with the changes that will be applied, run
terraform applyto execute Terraform.
Permissions Required for Deployment 📎
Agentless
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.enable |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.undelete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.operations.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.operations.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.access |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.add |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.destroy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.enable |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.objects.delete |
Agentless (Org Integration)
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | compute.projects.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.create |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.delete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.list |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.undelete |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | iam.roles.update |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.getIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | resourcemanager.organizations.setIamPolicy |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.quotas.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.get |
| organizations/<GOOGLECLOUD_ORG_ACCOUNT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.enable |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | cloudscheduler.jobs.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.undelete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.roles.update |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.jobs.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.operations.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | run.operations.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.secrets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.access |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.add |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.destroy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.enable |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | secretmanager.versions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.buckets.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | storage.objects.delete |
Permissions Used in Operation 📎
Agentless
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-orchestrate-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-orchestrate-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-scanner-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-scanner-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-sa-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-sa-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_orchestrate_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Cloud Run Jobs) | [ |
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_snapshot_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role for monitored project (Create Snapshots) | [ |
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_scanner_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Scanner Instance) | [ |
Agentless (Org Integration)
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-orchestrate-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-orchestrate-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-scanner-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-scanner-<UNIQUE_ID> | [ |
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lacework-awls-sa-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lacework-awls-sa-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_orchestrate_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Cloud Run Jobs) | [ |
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_scanner_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Scanner Instance) | [ |
| google_organization_iam_custom_role | organizations/<GCP_ORG_ACCOUNT>/roles/lacework_awls_snapshot_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role for monitored organization (Organization Snapshots) | [ |
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| User Entity Behaviour Analytics (UEBA) | Kubernetes Audit Log Dashboard Kubernetes Anomaly Detection Kubernetes Audit Log Polygraph | GKE Audit |
Prerequisites 📎
Overview
Lacework integrates with GKE Audit Logs in an event-based streaming pull mode for monitoring GKE admin read, data read, and data write events. This topic describes how to integrate with GKE by running Lacework Terraform modules from Google Cloud Shell.
If you are new to the Lacework Terraform provider, or Lacework Terraform modules, read Terraform for Lacework Overview to learn the basics on how to configure the provider and more.
Resources
Organization level integrations cover all existing projects in the organization, and automatically add any new projects added after the initial integration.
Project level integrations cover only specific projects and any new projects must be added as required.
To integrate at the organization or project level, Lacework requires the following resources be provisioned in Google Cloud:
- Google Cloud Project - A project to contain the required cloud resources with billing enabled. When integrating at the organization level, Lacework recommends that you create a project specifically for Lacework resources. When integrating at the project level, all required resources for Lacework may be provisioned within the project being integrated.
- Google Pub/Sub Topic - Topic for GKE Audit Logs events
- Google Pub/Sub Subscription - Subscription for Lacework to pull the GKE Audit Log events from
- Google Logging Sink - To export Cloud Audit Logs to the Pub/Sub topic
- Service Account for Lacework - A service account will be created to provide Lacework read-only access to Google Cloud Platform with the following roles:
- Project/Organization Level Integration
roles/pubsub.publisherroles/pubsub.subscriberroles/monitoring.viewer
- Project/Organization Level Integration
For organization level integrations, follow the steps in Integrate GKE Audit Logs at the Organization Level.
For project level integrations, follow the steps in Integrate GKE Audit Logs at the Project Level.
Requirements
Google Cloud Shell inherits the permissions of the user running Cloud Shell. Before beginning, determine whether the integration between Google Cloud and Lacework will be at the organization level or the project level, and then ensure the user account running Google Cloud Shell has the following permissions:
- Organization level integrations
roles/owner- For an organization level integration, Lacework recommends that you create a new project specifically for the Lacework resources. The user account used to run Google Cloud Shell must haveOwnerpermissions for that project.roles/resourcemanager.organizationAdminroles/iam.organizationRoleAdmin
- Project level integrations
roles/owner- For a project level integration, Lacework recommends that you use the project being integrated to provision the required resources. The user account used to run Google Cloud Shell must haveOwnerpermissions for every project being integrated into Lacework.
In addition to Google Cloud permissions, the Terraform provider for Lacework must be configured to authenticate with the Lacework API using a Lacework API key and secret access key. For more information on configuring the Terraform Provider for Lacework, visit Terraform for Lacework Overview.
Module Inputs Reference
For an up-to-date guide on all available configuration inputs, refer to the Terraform Registry documentation:
Module Dependencies
Lacework Terraform modules for GCP have the following dependencies that will be installed when running terraform init:
For detailed information on these dependencies, visit Lacework on the Terraform Registry.
Google Cloud Shell Configuration
Google Cloud Shell is an embedded terminal/command-line interface that you can use within the Google Console. Google Cloud Shell comes with tools pre-installed like the Google Cloud SDK, gcloud command-line tool, and Terraform pre-installed to manage and automate your projects and resources in your environment.
Lacework provides a robust command-line interface that generates Terraform code, installs the Terraform CLI (if not already installed), and can run Terraform inside Cloud Shell.
Ingested Logs
Lacework ingests Admin Activity logs and Data Access logs. Admin Activity logs are enabled by GCP by default. You may have to enable Data Access logs at an additional cost from GCP to access the following event groups:
- ADMIN_READ: access to Kubernetes metadata and configuration
- DATA_READ: access to Kubernetes resources
- DATA_WRITE: creation and changes to Kubernetes resources
- In the Google Cloud console, go to IAM & Admin > Audit Logs.
- In the Data Access audit logs configuration table next to Filter, start typing Kubernetes and select Kubernetes Engine API.
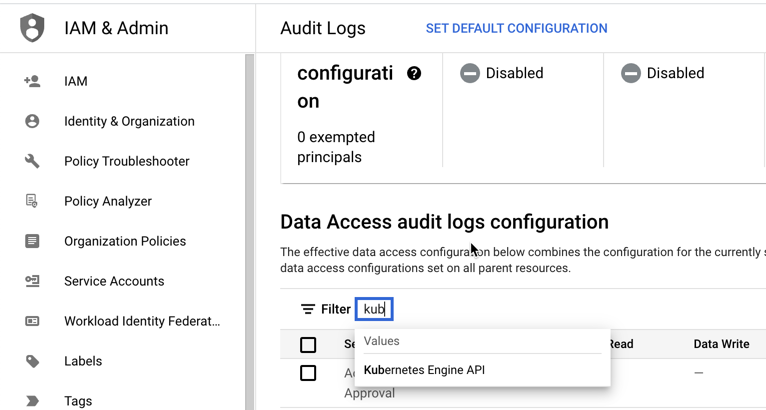
- With Kubernetes Engine API selected, select the logs and click Save.
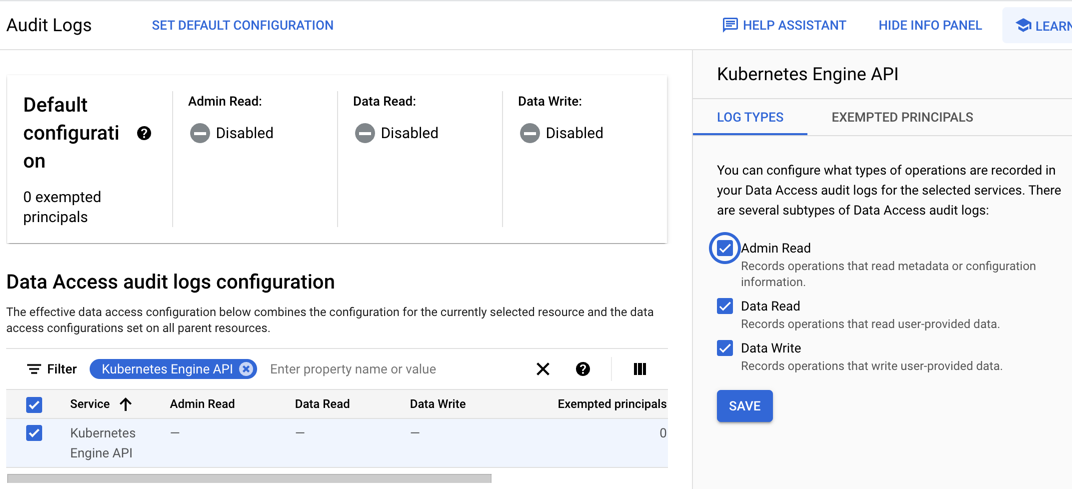
See the following Google Cloud documentation about Configure Data Access audit logs for additional details.
Permissions Required for Deployment 📎
GKE Audit
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | logging.sinks.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.subscriptions.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.attachSubscription |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | pubsub.topics.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
Permissions Used in Operation 📎
Agentless
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-gke-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-gke-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|---|---|---|
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_orchestrate_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Cloud Run Jobs) | [ |
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_snapshot_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role for monitored project (Create Snapshots) | [ |
| google_project_iam_custom_role | projects/<GCP_PROJECT>/roles/lacework_awls_scanner_<UNIQUE_ID> | Lacework Agentless Workload Scanning Role (Scanner Instance) | [ |
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | GCR |
Prerequisites 📎
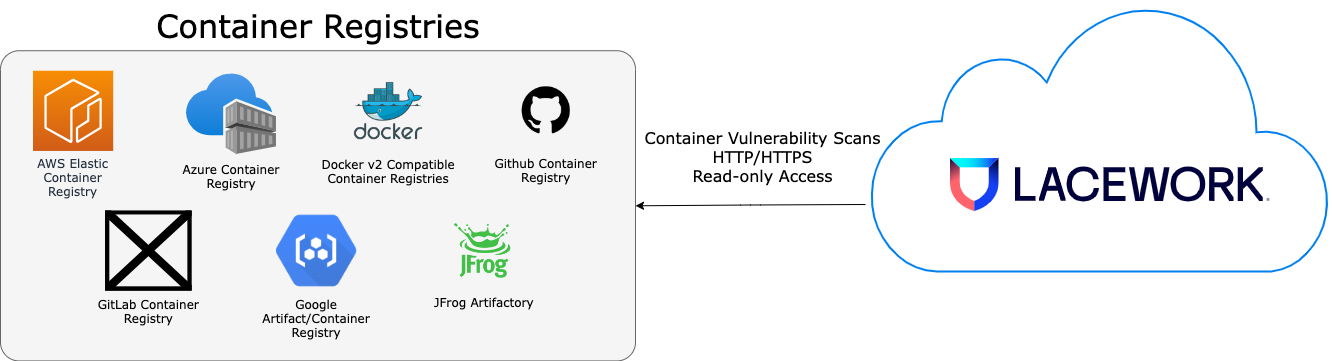
Container Registry Support
Google Container Registry (GCR) integrations support:
- Auto polling - polling occurs every 15 minutes.
- On-demand scans via the API.
Architecture 📎
Permissions Required for Deployment 📎
GCR
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | servicemanagement.services.bind |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | servicemanagement.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | servicemanagement.services.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.operations.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.operations.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.enable |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
Permissions Used in Operation 📎
GCR
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-gar-lw-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-gar-lw-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|
| Use Cases | Lacework Feature(s) | Data Source |
|---|---|---|
| Vulnerability Management | Vulnerability Management Dashboard | GAR |
Prerequisites 📎
Transition from Google Container Registry (GCR) to Google Artifact Registry (GAR)
Google Artifact Registry (GAR) is the evolution of Google Container Registry (GCR). As a fully managed service with support for both container images and non-container artifacts, GAR extends the capabilities of GCR.
For details on how to transition from GCR to GAR within Google Cloud Platform, see Transitioning from Container Registry.
Artifact Registry Support
GAR integrations support:
- Auto polling - polling occurs every 15 minutes.
- On-demand scans via the API.
Prerequisite
Before you configure Lacework, create a Google service account. For details, see Service accounts.
Architecture 📎
Permissions Required for Deployment 📎
GAR
The permissions outlined here are required when using the default terraform configuration and applicable to the target account for integration:| Scope | Permission |
|---|---|
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | compute.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccountKeys.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.create |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.delete |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | iam.serviceAccounts.list |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.getIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | resourcemanager.projects.setIamPolicy |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.quotas.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.get |
| projects/<LACEWORK_GOOGLECLOUD_PROJECT> | serviceusage.services.list |
Permissions Used in Operation 📎
GAR
ServiceAccounts
| Type | Name | Account | Display Name | Membership |
|---|---|---|---|---|
| google_service_account | projects/<GCP_PROJECT>/serviceAccounts/lw-gcr-lw-<UNIQUE_ID>@<GCP_PROJECT>.iam.gserviceaccount.com | projects/<GCP_PROJECT> | lw-gcr-lw-<UNIQUE_ID> | [ |
Roles
| Type | Name | Title | Permissions |
|---|